Phones
Latest about Phones
-
-
 Closing the gapSamsung could slowly trickle more missing Galaxy AI features on the Galaxy S25By Nickolas Diaz Published
Closing the gapSamsung could slowly trickle more missing Galaxy AI features on the Galaxy S25By Nickolas Diaz Published -
 Hello Fold!The best Motorola Razr Fold deals of May 2026 — the future of book-style foldables has arrivedBy Patrick Farmer Published
Hello Fold!The best Motorola Razr Fold deals of May 2026 — the future of book-style foldables has arrivedBy Patrick Farmer Published -
 UnbelievableI just scored a FREE Motorola Razr Fold with this new deal from T-Mobile — no trade-in requiredBy Patrick Farmer Published
UnbelievableI just scored a FREE Motorola Razr Fold with this new deal from T-Mobile — no trade-in requiredBy Patrick Farmer Published -
 Deals for dadsSamsung launches Father's Day sale with some of the year's best deals on the Galaxy S26 Ultra, Watch 8 Ultra, and beyondBy Patrick Farmer Published
Deals for dadsSamsung launches Father's Day sale with some of the year's best deals on the Galaxy S26 Ultra, Watch 8 Ultra, and beyondBy Patrick Farmer Published -
 Concerned about privacy on your Android? Here’s why Bitdefender is your all-in-one solutionBy Sponsored Published
Concerned about privacy on your Android? Here’s why Bitdefender is your all-in-one solutionBy Sponsored Published -
 Ace of baseMotorola Razr 2026 vs. Razr 2024: Is it finally time to upgrade?By Roydon Cerejo Published
Ace of baseMotorola Razr 2026 vs. Razr 2024: Is it finally time to upgrade?By Roydon Cerejo Published -
 Small declineThe US phone market struggled in Q1, but one Android maker made serious headwayBy Nickolas Diaz Published
Small declineThe US phone market struggled in Q1, but one Android maker made serious headwayBy Nickolas Diaz Published
-
Explore Phones
Apple iPhone
-
-
 Hold on, AppleApple reveals WWDC 26 in the shadow of Google I/OBy Nickolas Diaz Published
Hold on, AppleApple reveals WWDC 26 in the shadow of Google I/OBy Nickolas Diaz Published -
 Leadership changeApple's Tim Cook is stepping down as CEO later this year — here's the Apple veteran next upBy Brady Snyder Published
Leadership changeApple's Tim Cook is stepping down as CEO later this year — here's the Apple veteran next upBy Brady Snyder Published -
 How To4 Android phones you should buy instead of the iPhone 17eBy Brady Snyder Published
How To4 Android phones you should buy instead of the iPhone 17eBy Brady Snyder Published -
 iPhone vs. GalaxyiPhone 17e vs. Samsung Galaxy S25 FE: Simplicity or versatility?By Brady Snyder Published
iPhone vs. GalaxyiPhone 17e vs. Samsung Galaxy S25 FE: Simplicity or versatility?By Brady Snyder Published -
 Apple vs GoogleiPhone 17e vs. Google Pixel 10a: Two affordable flagships, one tough decisionBy Sanuj Bhatia Published
Apple vs GoogleiPhone 17e vs. Google Pixel 10a: Two affordable flagships, one tough decisionBy Sanuj Bhatia Published -
 Just as goodNeed to buy an iPhone in 2026? Here's why you should get the iPhone 17By Harish Jonnalagadda Published
Just as goodNeed to buy an iPhone in 2026? Here's why you should get the iPhone 17By Harish Jonnalagadda Published -
 Choices, choicesWith the iPhone 17 selling this well, I don't think Apple cares about low iPhone Air demandBy Brady Snyder Published
Choices, choicesWith the iPhone 17 selling this well, I don't think Apple cares about low iPhone Air demandBy Brady Snyder Published -
 HardwiredThe iPhone Air is the coolest phone I used in 2025By Harish Jonnalagadda Published
HardwiredThe iPhone Air is the coolest phone I used in 2025By Harish Jonnalagadda Published -
 Present or future?I tested the iPhone Air, and it finally lets you choose your compromiseBy Brady Snyder Published
Present or future?I tested the iPhone Air, and it finally lets you choose your compromiseBy Brady Snyder Published
-
Asus
-
-
 Bye for now, ASUSI'm going to miss new ASUS phones in 2026 for this one reasonBy Brady Snyder Published
Bye for now, ASUSI'm going to miss new ASUS phones in 2026 for this one reasonBy Brady Snyder Published -
 Finally!Asus ROG Phone 9 and Zenfone 12 Ultra users can now upgrade to Android 16By Brady Snyder Published
Finally!Asus ROG Phone 9 and Zenfone 12 Ultra users can now upgrade to Android 16By Brady Snyder Published -
 Game onASUS ROG Phone 9 Pro review: Ultimate bragging rightsBy Harish Jonnalagadda Last updated
Game onASUS ROG Phone 9 Pro review: Ultimate bragging rightsBy Harish Jonnalagadda Last updated -
 ContradictionsASUS Zenfone 12 Ultra review: I really like this phone, but you shouldn't buy itBy Harish Jonnalagadda Published
ContradictionsASUS Zenfone 12 Ultra review: I really like this phone, but you shouldn't buy itBy Harish Jonnalagadda Published -
 Zen-aestheticASUS reveals the Zenfone 12 Ultra with a spotless design and a powerful flagship chipBy Nickolas Diaz Published
Zen-aestheticASUS reveals the Zenfone 12 Ultra with a spotless design and a powerful flagship chipBy Nickolas Diaz Published -
 A little cheaperThe budget ASUS ROG Phone 9 FE is finally here with a 2023 chip and gaming AIBy Nickolas Diaz Published
A little cheaperThe budget ASUS ROG Phone 9 FE is finally here with a 2023 chip and gaming AIBy Nickolas Diaz Published -
 For the hopefulThe ASUS ROG Phone 9 'FE' is rumored to have a launch on the horizonBy Nickolas Diaz Published
For the hopefulThe ASUS ROG Phone 9 'FE' is rumored to have a launch on the horizonBy Nickolas Diaz Published -
 Ultimate ZenASUS Zenfone 11 Ultra review: Identity crisisBy Harish Jonnalagadda Published
Ultimate ZenASUS Zenfone 11 Ultra review: Identity crisisBy Harish Jonnalagadda Published -
 Asus ROG adds a new ultra-fast Wi-Fi 6E gaming router to its lineupBy Samuel Contreras Published
Asus ROG adds a new ultra-fast Wi-Fi 6E gaming router to its lineupBy Samuel Contreras Published
-
Carriers
-
-
 Dirt cheapNew Boost Mobile deal gives you a taste of Unlimited for ONLY $10/month — then $25/month for lifeBy Patrick Farmer Published
Dirt cheapNew Boost Mobile deal gives you a taste of Unlimited for ONLY $10/month — then $25/month for lifeBy Patrick Farmer Published -
 Magnificient Mint Mobile!Mint Mobile review: Tons of data with multi-month savingsBy Rajat Sharma Last updated
Magnificient Mint Mobile!Mint Mobile review: Tons of data with multi-month savingsBy Rajat Sharma Last updated -
 Travel in comfortThese 6 prepaid SIM cards for US tourists will take your 2026 travels to the next levelBy Rajat Sharma Last updated
Travel in comfortThese 6 prepaid SIM cards for US tourists will take your 2026 travels to the next levelBy Rajat Sharma Last updated -
 Intelligent NetworkT-Mobile's network-native AI Live Translation beta is here, and this is just the startBy Nickolas Diaz Published
Intelligent NetworkT-Mobile's network-native AI Live Translation beta is here, and this is just the startBy Nickolas Diaz Published -
 Go prepaid, save more!What is the best MVNO for Android users? We tested the top-rated prepaid carriers, and this is what we foundBy Patrick Farmer Last updated
Go prepaid, save more!What is the best MVNO for Android users? We tested the top-rated prepaid carriers, and this is what we foundBy Patrick Farmer Last updated -
 Unlimited access!Best unlimited data plans of 2026: Verizon, Mint Mobile, and beyondBy Patrick Farmer Last updated
Unlimited access!Best unlimited data plans of 2026: Verizon, Mint Mobile, and beyondBy Patrick Farmer Last updated -
 4 for freeYes, it's real — new Verizon deal gives your family four free phones AND unlimited wireless for only $25 per lineBy Patrick Farmer Published
4 for freeYes, it's real — new Verizon deal gives your family four free phones AND unlimited wireless for only $25 per lineBy Patrick Farmer Published -
 Bye-bye fees!New Verizon deal is waiving activation fees on ALL phones for a limited time — here's what you need to knowBy Patrick Farmer Published
Bye-bye fees!New Verizon deal is waiving activation fees on ALL phones for a limited time — here's what you need to knowBy Patrick Farmer Published -
 Make the switchReady for a change? Switch from AT&T or Verizon and T-Mobile will give you up to $800 to pay off your phoneBy Patrick Farmer Published
Make the switchReady for a change? Switch from AT&T or Verizon and T-Mobile will give you up to $800 to pay off your phoneBy Patrick Farmer Published
-
Google Fi
-
-
 It's not just youIf your Google Fi says your SIM isn't active, here's what's going onBy Sanuj Bhatia Published
It's not just youIf your Google Fi says your SIM isn't active, here's what's going onBy Sanuj Bhatia Published -
 Lots of choices!The best Google Fi Wireless alternatives in 2026By Samuel Contreras Last updated
Lots of choices!The best Google Fi Wireless alternatives in 2026By Samuel Contreras Last updated -
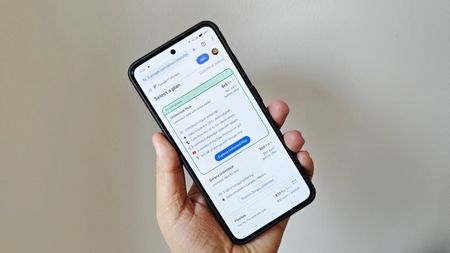 Save with Fi!Google Fi Wireless plans, deals, and prices: everything you need to knowBy Samuel Contreras Last updated
Save with Fi!Google Fi Wireless plans, deals, and prices: everything you need to knowBy Samuel Contreras Last updated -
 AI power-upGoogle Fi is using AI to make your phone service less annoyingBy Jay Bonggolto Published
AI power-upGoogle Fi is using AI to make your phone service less annoyingBy Jay Bonggolto Published -
 Sharing is caring!Which MVNOs allow tethering?By Samuel Contreras Last updated
Sharing is caring!Which MVNOs allow tethering?By Samuel Contreras Last updated -
 Tenth anniversaryGoogle Fi celebrates 10 years with a new affordable plan to take on T-MobileBy Vishnu Sarangapurkar Published
Tenth anniversaryGoogle Fi celebrates 10 years with a new affordable plan to take on T-MobileBy Vishnu Sarangapurkar Published -
 Ask JerryAsk Jerry: Will my phone work outside of the US?By Jerry Hildenbrand Published
Ask JerryAsk Jerry: Will my phone work outside of the US?By Jerry Hildenbrand Published -
 Pixel 8a spottedThe Pixel 8a may have just appeared in a Google Fi Wireless adBy Vishnu Sarangapurkar Published
Pixel 8a spottedThe Pixel 8a may have just appeared in a Google Fi Wireless adBy Vishnu Sarangapurkar Published -
 Two Great Options!Tello vs. Google Fi: Which flexible prepaid carrier is the best?By Samuel Contreras Last updated
Two Great Options!Tello vs. Google Fi: Which flexible prepaid carrier is the best?By Samuel Contreras Last updated
-
Google Pixel
-
-
 ProblematicOriginal Pixel Fold suffers a display blackout that pins this patch as the culpritBy Nickolas Diaz Published
ProblematicOriginal Pixel Fold suffers a display blackout that pins this patch as the culpritBy Nickolas Diaz Published -
 Teaser or not?Wait—was that a Pixel 11 teaser? Theories are buzzing after Google's I/OBy Nickolas Diaz Published
Teaser or not?Wait—was that a Pixel 11 teaser? Theories are buzzing after Google's I/OBy Nickolas Diaz Published -
 Live BlogGoogle I/O 2026 Live Blog updates: Android 17, Android XR glasses, Gemini AI newsBy Derrek Lee Last updated
Live BlogGoogle I/O 2026 Live Blog updates: Android 17, Android XR glasses, Gemini AI newsBy Derrek Lee Last updated -
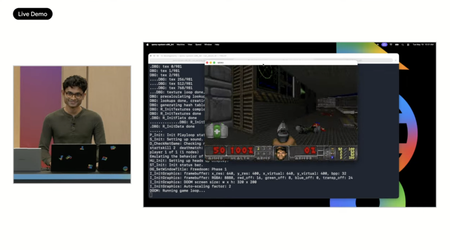 MacBook at Google???Did Google use a MacBook during its live demo at Google I/O?By Shruti Shekar Published
MacBook at Google???Did Google use a MacBook during its live demo at Google I/O?By Shruti Shekar Published -
 Pixel PerfectBest Google Pixel phonesBy Andrew Myrick Last updated
Pixel PerfectBest Google Pixel phonesBy Andrew Myrick Last updated -
 Pixel DealsDitch your old phone with the 44% OFF the the Google Pixel 9 — or its biggest price drop yetBy Zachary David Published
Pixel DealsDitch your old phone with the 44% OFF the the Google Pixel 9 — or its biggest price drop yetBy Zachary David Published -
 How to tune inGoogle I/O 2026: How to stream and what to expect from the eventBy Sanuj Bhatia Last updated
How to tune inGoogle I/O 2026: How to stream and what to expect from the eventBy Sanuj Bhatia Last updated -
 It learns your lifeGoogle just turned your Pixel 10 into a phone that thinks ahead for youBy Jay Bonggolto Published
It learns your lifeGoogle just turned your Pixel 10 into a phone that thinks ahead for youBy Jay Bonggolto Published -
 Android Central LabsThis brand-new Pixel display feature is delivering comfort in a unique wayBy Nicholas Sutrich Published
Android Central LabsThis brand-new Pixel display feature is delivering comfort in a unique wayBy Nicholas Sutrich Published
-
Honor
-
-
 Launch officialHonor just gave us a clearer idea of when its Robot Phone is comingBy Sanuj Bhatia Published
Launch officialHonor just gave us a clearer idea of when its Robot Phone is comingBy Sanuj Bhatia Published -
 Looking to competeHonor, Vivo might've started on 'Wide' foldables to compete with SamsungBy Nickolas Diaz Published
Looking to competeHonor, Vivo might've started on 'Wide' foldables to compete with SamsungBy Nickolas Diaz Published -
 Android MagicHonor for Android 17 Beta 3 sees developers get on board with the Magic 8 ProBy Nickolas Diaz Published
Android MagicHonor for Android 17 Beta 3 sees developers get on board with the Magic 8 ProBy Nickolas Diaz Published -
 Flashy distractionsHonor 600 series hits the UK with big discounts and a pop culture makeoverBy Jay Bonggolto Published
Flashy distractionsHonor 600 series hits the UK with big discounts and a pop culture makeoverBy Jay Bonggolto Published -
 It's magicHonor Connect, photography updates carry the Magic 8 Pro's huge April patchBy Nickolas Diaz Published
It's magicHonor Connect, photography updates carry the Magic 8 Pro's huge April patchBy Nickolas Diaz Published -
 Good stuffHonor 600 Pro review: This phone is so good that it surprised meBy Nirave Gondhia Published
Good stuffHonor 600 Pro review: This phone is so good that it surprised meBy Nirave Gondhia Published -
 What an honorHonor 600 review: Flagship feels, mid-range priceBy Nicholas Sutrich Published
What an honorHonor 600 review: Flagship feels, mid-range priceBy Nicholas Sutrich Published -
 New Honor phoneThe new Honor 600 series brings flagship cameras and upgraded AI featuresBy Nirave Gondhia Published
New Honor phoneThe new Honor 600 series brings flagship cameras and upgraded AI featuresBy Nirave Gondhia Published -
 The thin phone of your dreamsThe Magic 8 Pro Air proves that Apple and Samsung got their thin phones wrongBy Nirave Gondhia Published
The thin phone of your dreamsThe Magic 8 Pro Air proves that Apple and Samsung got their thin phones wrongBy Nirave Gondhia Published
-
Huawei
-
-
 Wide is the new tallThe wide foldable is finally here, and it didn’t come from SamsungBy Jay Bonggolto Published
Wide is the new tallThe wide foldable is finally here, and it didn’t come from SamsungBy Jay Bonggolto Published -
 Soaring aboveI used Huawei's Mate X7 to take photos of the world's tallest building, and I'm convinced that this foldable has the best camerasBy Harish Jonnalagadda Published
Soaring aboveI used Huawei's Mate X7 to take photos of the world's tallest building, and I'm convinced that this foldable has the best camerasBy Harish Jonnalagadda Published -
 Coming BackHuawei's alleged Mate XT sequel might have some spicy upgrades up its sleeveBy Nickolas Diaz Published
Coming BackHuawei's alleged Mate XT sequel might have some spicy upgrades up its sleeveBy Nickolas Diaz Published -
 What could it be?Jackie Chan was spotted using a foldable on TikTok, and we've got our top suspectsBy Nandika Ravi Published
What could it be?Jackie Chan was spotted using a foldable on TikTok, and we've got our top suspectsBy Nandika Ravi Published -
 The bestHuawei Mate XT camera review: Putting all other foldables to shameBy Harish Jonnalagadda Published
The bestHuawei Mate XT camera review: Putting all other foldables to shameBy Harish Jonnalagadda Published -
 Why not both?Huawei's new flip phone blurs the line between foldablesBy Nickolas Diaz Published
Why not both?Huawei's new flip phone blurs the line between foldablesBy Nickolas Diaz Published -
 Leveling upHuawei's tri-fold Mate XT is the most exciting phone I've used in a long timeBy Harish Jonnalagadda Published
Leveling upHuawei's tri-fold Mate XT is the most exciting phone I've used in a long timeBy Harish Jonnalagadda Published -
 Best Huawei phones 2022By Harish Jonnalagadda Last updated
Best Huawei phones 2022By Harish Jonnalagadda Last updated -
 Huawei's 'Super Device' is greater than the sum of its partsBy Alex Dobie Published
Huawei's 'Super Device' is greater than the sum of its partsBy Alex Dobie Published
-
MediaTek
-
-
 Powered-upMediaTek's Dimensity 9500s, 8500 surge with power for even more Android phonesBy Nickolas Diaz Published
Powered-upMediaTek's Dimensity 9500s, 8500 surge with power for even more Android phonesBy Nickolas Diaz Published -
 OVER 9000MediaTek's new powerhouse chip is the unicorn you'll never get to seeBy Jerry Hildenbrand Published
OVER 9000MediaTek's new powerhouse chip is the unicorn you'll never get to seeBy Jerry Hildenbrand Published -
 Flagship powerThe MediaTek Dimensity 9500 is the Android powerhouse you'd expectBy Michael L Hicks Published
Flagship powerThe MediaTek Dimensity 9500 is the Android powerhouse you'd expectBy Michael L Hicks Published -
 Chip launch confirmedMediaTek confirms the date for its next flagship chip launch, and the timing is interestingBy Sanuj Bhatia Published
Chip launch confirmedMediaTek confirms the date for its next flagship chip launch, and the timing is interestingBy Sanuj Bhatia Published -
 Early DaysVery early MediaTek Dimensity 9500 benchmark leaves us waiting for moreBy Nickolas Diaz Published
Early DaysVery early MediaTek Dimensity 9500 benchmark leaves us waiting for moreBy Nickolas Diaz Published -
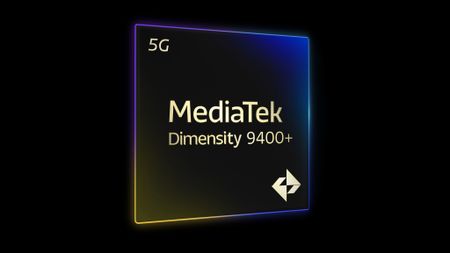 Agentic AIMediaTek highlights Dimensity 9400 Plus with edge-AI specs and 20% boost in Gen AIBy Nickolas Diaz Published
Agentic AIMediaTek highlights Dimensity 9400 Plus with edge-AI specs and 20% boost in Gen AIBy Nickolas Diaz Published -
 Next-gen processorMediaTek's Kompanio Ultra will 'redefine' Chromebook Plus performance and AIBy Nickolas Diaz Published
Next-gen processorMediaTek's Kompanio Ultra will 'redefine' Chromebook Plus performance and AIBy Nickolas Diaz Published -
 MediaTek unveils Dimensity 700 for budget 5G phones and a 6nm Chromebook chipsetBy Harish Jonnalagadda Published
MediaTek unveils Dimensity 700 for budget 5G phones and a 6nm Chromebook chipsetBy Harish Jonnalagadda Published
-
Motorola
-
-
 Hello Fold!The best Motorola Razr Fold deals of May 2026 — the future of book-style foldables has arrivedBy Patrick Farmer Published
Hello Fold!The best Motorola Razr Fold deals of May 2026 — the future of book-style foldables has arrivedBy Patrick Farmer Published -
 UnbelievableI just scored a FREE Motorola Razr Fold with this new deal from T-Mobile — no trade-in requiredBy Patrick Farmer Published
UnbelievableI just scored a FREE Motorola Razr Fold with this new deal from T-Mobile — no trade-in requiredBy Patrick Farmer Published -
 Ace of baseMotorola Razr 2026 vs. Razr 2024: Is it finally time to upgrade?By Roydon Cerejo Published
Ace of baseMotorola Razr 2026 vs. Razr 2024: Is it finally time to upgrade?By Roydon Cerejo Published -
 A problemMotorola slid affiliate codes into your Amazon orders, now states this was 'unintended'By Nickolas Diaz Published
A problemMotorola slid affiliate codes into your Amazon orders, now states this was 'unintended'By Nickolas Diaz Published -
 A bigger foldMotorola Razr Fold: Release date, specs, features, and everything you need to knowBy Derrek Lee Last updated
A bigger foldMotorola Razr Fold: Release date, specs, features, and everything you need to knowBy Derrek Lee Last updated -
 Ultra goodnessIt was already hard to recommend the Motorola Razr Ultra (2026), but this $600 discount on last year's version makes it even harderBy Patrick Farmer Published
Ultra goodnessIt was already hard to recommend the Motorola Razr Ultra (2026), but this $600 discount on last year's version makes it even harderBy Patrick Farmer Published -
 Straight savingsNew AT&T deal gets you the Motorola Razr Plus 2026 for the price of a cup of coffee every month — no trade-in required!By Patrick Farmer Published
Straight savingsNew AT&T deal gets you the Motorola Razr Plus 2026 for the price of a cup of coffee every month — no trade-in required!By Patrick Farmer Published -
 Stealth upgradeMotorola Razr Plus 2026 review: Old Razr, new tricksBy Nicholas Sutrich Published
Stealth upgradeMotorola Razr Plus 2026 review: Old Razr, new tricksBy Nicholas Sutrich Published -
 Stylus tips and tricks6 things you can do with the Moto Pen Ultra on the Razr FoldBy Brady Snyder Published
Stylus tips and tricks6 things you can do with the Moto Pen Ultra on the Razr FoldBy Brady Snyder Published
-
Nothing
-
-
 Is it a dynasty?Chatter says Nothing's CMF Phone 3 Pro is delayed, specs and launch leakBy Nickolas Diaz Published
Is it a dynasty?Chatter says Nothing's CMF Phone 3 Pro is delayed, specs and launch leakBy Nickolas Diaz Published -
 Finally!The 'fantastic' Nothing Phone (3) is one of the most eye-catching devices on the market — and it just scored a major discount at Best BuyBy Patrick Farmer Published
Finally!The 'fantastic' Nothing Phone (3) is one of the most eye-catching devices on the market — and it just scored a major discount at Best BuyBy Patrick Farmer Published -
 AC HacksUnlock the hidden potential of your Nothing Phone 4a Pro with these 4 Essential tips and tricksBy Nicholas Sutrich Published
AC HacksUnlock the hidden potential of your Nothing Phone 4a Pro with these 4 Essential tips and tricksBy Nicholas Sutrich Published -
 Android Central LabsNothing's Essential Voice redefined how I talk to my phone, and it's about time someone fixed this problemBy Nicholas Sutrich Published
Android Central LabsNothing's Essential Voice redefined how I talk to my phone, and it's about time someone fixed this problemBy Nicholas Sutrich Published -
 Your voiceNothing's giving its phones an Essential Voice to usher in smarter transcriptionsBy Nickolas Diaz Published
Your voiceNothing's giving its phones an Essential Voice to usher in smarter transcriptionsBy Nickolas Diaz Published -
 The SIM tool trapThe Nothing Phone 4a Pro is nearly unbreakable, except for one design flawBy Jay Bonggolto Published
The SIM tool trapThe Nothing Phone 4a Pro is nearly unbreakable, except for one design flawBy Jay Bonggolto Published -
 Not AirDropNothing's new tool makes sharing between Android and desktop easier — and it does one thing differently [Update]By Sanuj Bhatia Published
Not AirDropNothing's new tool makes sharing between Android and desktop easier — and it does one thing differently [Update]By Sanuj Bhatia Published -
 Nothing vs GoogleNothing Phone 4a Pro vs. Google Pixel 10a: A style-first phone vs a smarter oneBy Sanuj Bhatia Published
Nothing vs GoogleNothing Phone 4a Pro vs. Google Pixel 10a: A style-first phone vs a smarter oneBy Sanuj Bhatia Published -
 Nothing beats a PixelNothing Phone 4a Pro review: The right phone at the right timeBy Nicholas Sutrich Published
Nothing beats a PixelNothing Phone 4a Pro review: The right phone at the right timeBy Nicholas Sutrich Published
-
Oneplus
-
-
 Android tablet done rightI used the OnePlus Pad 4 for three weeks — Here are 5 things I learnedBy Sanuj Bhatia Published
Android tablet done rightI used the OnePlus Pad 4 for three weeks — Here are 5 things I learnedBy Sanuj Bhatia Published -
 damage controlYour OnePlus update is on hold, and honestly, you should be gladBy Jay Bonggolto Published
damage controlYour OnePlus update is on hold, and honestly, you should be gladBy Jay Bonggolto Published -
 Straight savingsThe OnePlus 15R is a battery life beast, and it just scored a record-smashing discount at AmazonBy Patrick Farmer Published
Straight savingsThe OnePlus 15R is a battery life beast, and it just scored a record-smashing discount at AmazonBy Patrick Farmer Published -
 Still fresh, still coolOxygenOS 16.1 unlocks a smarter, more secure and personal OnePlus 15By Nickolas Diaz Published
Still fresh, still coolOxygenOS 16.1 unlocks a smarter, more secure and personal OnePlus 15By Nickolas Diaz Published -
 Merged?Major reports say OnePlus, Realme merge, but there's a lot still in the darkBy Nickolas Diaz Published
Merged?Major reports say OnePlus, Realme merge, but there's a lot still in the darkBy Nickolas Diaz Published -
 Press StartYeah, the OnePlus Ace 6 Ultra is a phone, but it's mimicking handheld consolesBy Nickolas Diaz Published
Press StartYeah, the OnePlus Ace 6 Ultra is a phone, but it's mimicking handheld consolesBy Nickolas Diaz Published -
 Not looking goodOnePlus' Europe exit isn't official yet, but the signs aren't greatBy Sanuj Bhatia Published
Not looking goodOnePlus' Europe exit isn't official yet, but the signs aren't greatBy Sanuj Bhatia Published -
 OnePlus Nord 6 review: The endurance champion of 2026By Harish Jonnalagadda Published
OnePlus Nord 6 review: The endurance champion of 2026By Harish Jonnalagadda Published -
 Never settleBest OnePlus phones 2026By Harish Jonnalagadda Last updated
Never settleBest OnePlus phones 2026By Harish Jonnalagadda Last updated
-
Oppo
-
-
 Finally expandingAirDrop sharing appears to be expanding beyond Pixel and Galaxy phonesBy Sanuj Bhatia Published
Finally expandingAirDrop sharing appears to be expanding beyond Pixel and Galaxy phonesBy Sanuj Bhatia Published -
 Sort it outI finally got a handle on my expenses thanks to this AI feature on the Find X9 UltraBy Harish Jonnalagadda Published
Sort it outI finally got a handle on my expenses thanks to this AI feature on the Find X9 UltraBy Harish Jonnalagadda Published -
 OPPO Find X9 Ultra review: This world-class camera is also a phoneBy Harish Jonnalagadda Published
OPPO Find X9 Ultra review: This world-class camera is also a phoneBy Harish Jonnalagadda Published -
 OPPO Find X9 Ultra hands-on: Is this the best camera phone of 2026?By Harish Jonnalagadda Published
OPPO Find X9 Ultra hands-on: Is this the best camera phone of 2026?By Harish Jonnalagadda Published -
 Just look at itOPPO's Reno 15 Pro and Reno 15 are the flagship killers you deserve in 2026By Harish Jonnalagadda Published
Just look at itOPPO's Reno 15 Pro and Reno 15 are the flagship killers you deserve in 2026By Harish Jonnalagadda Published -
 Finding OPPOOPPO Find N6 vs. Samsung Galaxy Z Fold 7: We have a clear winnerBy Roydon Cerejo Published
Finding OPPOOPPO Find N6 vs. Samsung Galaxy Z Fold 7: We have a clear winnerBy Roydon Cerejo Published -
 Ultra worldwideOPPO puts the Find X9 Ultra and 'global' in the same sentence, teases April debutBy Nickolas Diaz Published
Ultra worldwideOPPO puts the Find X9 Ultra and 'global' in the same sentence, teases April debutBy Nickolas Diaz Published -
 How ToOPPO's Find N6 foldable has a unique multitasking feature that Google needs to steal immediatelyBy Harish Jonnalagadda Published
How ToOPPO's Find N6 foldable has a unique multitasking feature that Google needs to steal immediatelyBy Harish Jonnalagadda Published -
 Finding greatnessOPPO Find N6 review: The next step in foldable evolutionBy Harish Jonnalagadda Published
Finding greatnessOPPO Find N6 review: The next step in foldable evolutionBy Harish Jonnalagadda Published
-
Qualcomm
-
-
 Grab some chipsQualcomm unveils a pair of chips: Snapdragon 6, 4 series to improve the features you actually useBy Nickolas Diaz Published
Grab some chipsQualcomm unveils a pair of chips: Snapdragon 6, 4 series to improve the features you actually useBy Nickolas Diaz Published -
 Qualcomm FY Q2 2026 earnings highlight a mobile industry under pressure from the memory shortageBy Derrek Lee Published
Qualcomm FY Q2 2026 earnings highlight a mobile industry under pressure from the memory shortageBy Derrek Lee Published -
 Elite, Pro, hello!Snapdragon 8 Elite Gen 6 CPU rumors join the 'powerful' 6 Pro in this early reportBy Nickolas Diaz Published
Elite, Pro, hello!Snapdragon 8 Elite Gen 6 CPU rumors join the 'powerful' 6 Pro in this early reportBy Nickolas Diaz Published -
 How To4 ways Snapdragon Wear Elite will make your next wearable more usefulBy Brady Snyder Published
How To4 ways Snapdragon Wear Elite will make your next wearable more usefulBy Brady Snyder Published -
 Smarter watches aheadQualcomm's new Snapdragon Wear Elite wants to make AI wearables actually smartBy Sanuj Bhatia Published
Smarter watches aheadQualcomm's new Snapdragon Wear Elite wants to make AI wearables actually smartBy Sanuj Bhatia Published -
 all-in-one connectivity chipQualcomm's Wi-Fi 8 chips are here, and they actually fix the stuff that annoys youBy Jay Bonggolto Published
all-in-one connectivity chipQualcomm's Wi-Fi 8 chips are here, and they actually fix the stuff that annoys youBy Jay Bonggolto Published -
 Faster speedsQualcomm's X105 modem will keep you connected in elevators and parking garagesBy Brady Snyder Published
Faster speedsQualcomm's X105 modem will keep you connected in elevators and parking garagesBy Brady Snyder Published -
 EarningsQualcomm reports record earnings, but things aren't looking goodBy Derrek Lee Published
EarningsQualcomm reports record earnings, but things aren't looking goodBy Derrek Lee Published -
 Elite... is also Pro?Qualcomm's next 'Elite' Snapdragon could go Pro for this year's flagshipsBy Nickolas Diaz Published
Elite... is also Pro?Qualcomm's next 'Elite' Snapdragon could go Pro for this year's flagshipsBy Nickolas Diaz Published
-
RedMagic
-
-
 Liquid CooledRedMagic's 11S Pro is a gaming beast, and it's crazy to think Liquid Cooling is in this phoneBy Nickolas Diaz Published
Liquid CooledRedMagic's 11S Pro is a gaming beast, and it's crazy to think Liquid Cooling is in this phoneBy Nickolas Diaz Published -
 fresh faceRedMagic 11 Air Trace Edition is the same great gaming phone in a louder shirtBy Jay Bonggolto Published
fresh faceRedMagic 11 Air Trace Edition is the same great gaming phone in a louder shirtBy Jay Bonggolto Published -
 How ToThese four features make the Redmagic 11 Air a beast of a gaming phoneBy Harish Jonnalagadda Published
How ToThese four features make the Redmagic 11 Air a beast of a gaming phoneBy Harish Jonnalagadda Published -
 Slimmer, not weakerThe RedMagic 11 Air is surprisingly thin, and I’m obsessed with its massive 7,000mAh batteryBy Jay Bonggolto Published
Slimmer, not weakerThe RedMagic 11 Air is surprisingly thin, and I’m obsessed with its massive 7,000mAh batteryBy Jay Bonggolto Published -
 What're we playing?RedMagic 11 Air is a cool, crisp mobile gaming guru with the series' biggest 7,000mAh batteryBy Nickolas Diaz Published
What're we playing?RedMagic 11 Air is a cool, crisp mobile gaming guru with the series' biggest 7,000mAh batteryBy Nickolas Diaz Published -
 Cooling ReimaginedRedMagic just dropped a gaming phone with a literal water cooler insideBy Jay Bonggolto Published
Cooling ReimaginedRedMagic just dropped a gaming phone with a literal water cooler insideBy Jay Bonggolto Published -
 Stylish powerRedmagic 10S Pro review: Beating ASUS at its own gameBy Harish Jonnalagadda Published
Stylish powerRedmagic 10S Pro review: Beating ASUS at its own gameBy Harish Jonnalagadda Published -
 Game TimeThere may be a REDMAGIC gaming tablet on the horizon with a smaller screenBy Nickolas Diaz Published
Game TimeThere may be a REDMAGIC gaming tablet on the horizon with a smaller screenBy Nickolas Diaz Published -
 sleek and powerfulRedMagic's latest gaming phone is smart and powerful without the bulkBy Jay Bonggolto Published
sleek and powerfulRedMagic's latest gaming phone is smart and powerful without the bulkBy Jay Bonggolto Published
-
Samsung Galaxy
-
-
 Closing the gapSamsung could slowly trickle more missing Galaxy AI features on the Galaxy S25By Nickolas Diaz Published
Closing the gapSamsung could slowly trickle more missing Galaxy AI features on the Galaxy S25By Nickolas Diaz Published -
 Deals for dadsSamsung launches Father's Day sale with some of the year's best deals on the Galaxy S26 Ultra, Watch 8 Ultra, and beyondBy Patrick Farmer Published
Deals for dadsSamsung launches Father's Day sale with some of the year's best deals on the Galaxy S26 Ultra, Watch 8 Ultra, and beyondBy Patrick Farmer Published -
 Digital passportForgot your ID at home? Don't worry — Here's how to use your Samsung Galaxy phone as a digital passport at TSA checkpointsBy Sanuj Bhatia Published
Digital passportForgot your ID at home? Don't worry — Here's how to use your Samsung Galaxy phone as a digital passport at TSA checkpointsBy Sanuj Bhatia Published -
 Prices going upThinking of buying a Samsung flagship? You may not want to wait too longBy Sanuj Bhatia Published
Prices going upThinking of buying a Samsung flagship? You may not want to wait too longBy Sanuj Bhatia Published -
 Wasting no timeSamsung speeds ahead, rolls out One UI 9 Beta 2 for the Galaxy S26 overseasBy Nickolas Diaz Published
Wasting no timeSamsung speeds ahead, rolls out One UI 9 Beta 2 for the Galaxy S26 overseasBy Nickolas Diaz Published -
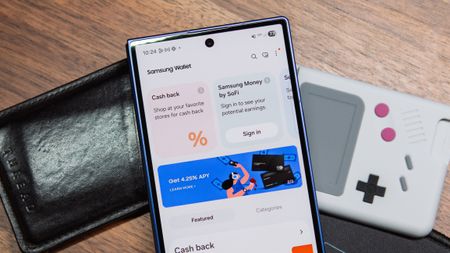 Digital passportsYour Samsung phone is officially a TSA-approved digital passportBy Jay Bonggolto Published
Digital passportsYour Samsung phone is officially a TSA-approved digital passportBy Jay Bonggolto Published -
 GoneAfter waiting for One UI 8.5, users say Samsung axed video featuresBy Nickolas Diaz Published
GoneAfter waiting for One UI 8.5, users say Samsung axed video featuresBy Nickolas Diaz Published -
 Naming ConundrumGalaxy Z Fold 8 rumors throw 'Ultra' into the mix, and it's got our heads spinningBy Nickolas Diaz Published
Naming ConundrumGalaxy Z Fold 8 rumors throw 'Ultra' into the mix, and it's got our heads spinningBy Nickolas Diaz Published -
 Still a concept or no?Leaked 'Galaxy Z Rollable' patent certainly is different, but not unheard of for SamsungBy Nickolas Diaz Published
Still a concept or no?Leaked 'Galaxy Z Rollable' patent certainly is different, but not unheard of for SamsungBy Nickolas Diaz Published
-
More about Phones
-
-
 Small declineThe US phone market struggled in Q1, but one Android maker made serious headwayBy Nickolas Diaz Published
Small declineThe US phone market struggled in Q1, but one Android maker made serious headwayBy Nickolas Diaz Published -
 Digital passportForgot your ID at home? Don't worry — Here's how to use your Samsung Galaxy phone as a digital passport at TSA checkpointsBy Sanuj Bhatia Published
Digital passportForgot your ID at home? Don't worry — Here's how to use your Samsung Galaxy phone as a digital passport at TSA checkpointsBy Sanuj Bhatia Published -
 A problemMotorola slid affiliate codes into your Amazon orders, now states this was 'unintended'By Nickolas Diaz Published
A problemMotorola slid affiliate codes into your Amazon orders, now states this was 'unintended'By Nickolas Diaz Published
-