We've tried every Samsung phone, and these are the best picks for you to buy in 2026
The best Samsung phones in 2026 focus on the company's strengths, like long software support promises, great features, and top-notch hardware quality.

Android Central has been around longer than Samsung's Galaxy series of smartphones, and we have tried every single model since their release. We know how to tell which ones are great and worth your money, and we've put them all through their paces, from the Samsung Galaxy S26 series to the Galaxy Z Fold 7.
The most up-to-date features and powerful software, along with the sleekest hardware, comes with the Galaxy S26 Ultra. We can't count out the classic Galaxy S26 and Galaxy S26 Plus, either. While we haven't seen a new "Edge" variant yet, the Galaxy S25 Edge is still available as a slimmer, lighter, and cheaper option that's still premium.
Samsung is firing on all cylinders when foldables are concerned, and the Galaxy Z Fold 7 and Galaxy Z Flip 7 are some of its best folding smartphones yet. The newest member of the party is the Galaxy Z TriFold, which costs $2,900 and packs a 10-inch foldable screen inside.
Between the reliable Galaxy S series, folding Galaxy Z series, and budget Galaxy A series, there's sure to be something for everyone here. Let's break down all our picks for the best Samsung phones below.
At a glance

Best overall
Samsung's latest Galaxy S26 Ultra includes a blazing-fast Snapdragon 8 Elite Gen 5 for Galaxy processor, which enables brand-new Galaxy AI features. It has a 6.9-inch screen with a Privacy Display feature and S Pen support. Plus, there are new rear camera sensors with wider apertures.

Best flagship
The Samsung Galaxy S26 might look the same as the earlier models, but there are some neat changes under-the-hood. It starts with the Snapdragon 8 Elite Gen 5 for Galaxy processor and a larger 6.3-inch display.

Best foldable
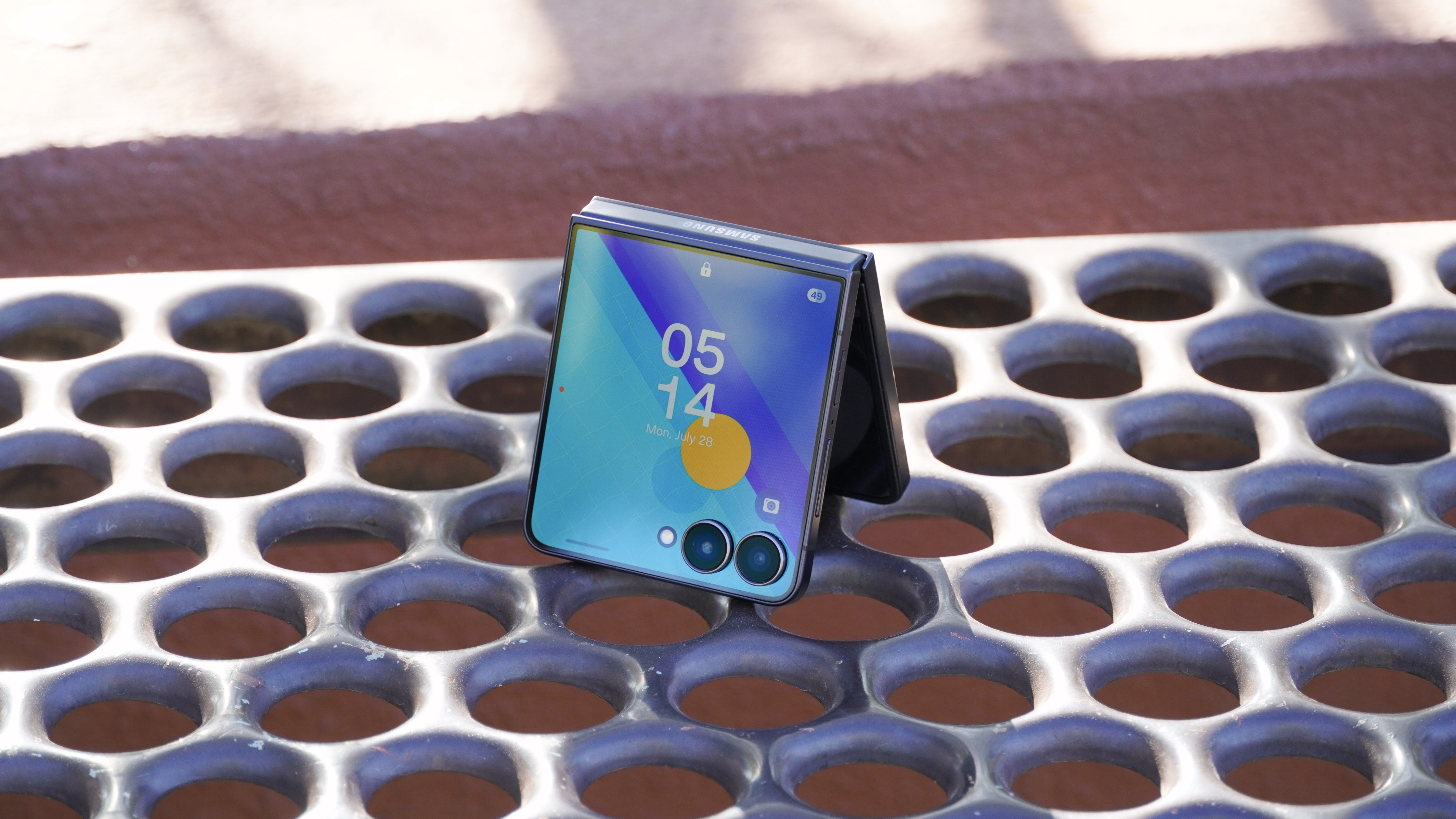
The larger, edge-to-edge cover screen and wider main screen on the Galaxy Z Flip 7 might be enough to make this the perfect foldable for everyone. It's more durable than ever, with an IP48 certification and a new hinge design.

Best premium foldable
The Samsung Galaxy Z Fold 7 features a redesigned chassis that's thinner and lighter than ever before, all while adding crucial processor and camera upgrades. With a wider cover screen, the foldable is now just as versatile opened or closed.

Best mid-range Galaxy
Mid-range refers more to the price here than the phone itself because the Galaxy A57 gives you a great camera, outstanding battery life, water and dust proofing, and expandable storage in a phone that costs around $500.

Best budget Galaxy
Whether you want something cheap for the jobsite or just don't need a ton of performance out of your phone, the Galaxy A17 is a strong budget pick with a nice screen, decent main camera, and 5G support.
Best overall

Specifications
Reasons to buy
Reasons to avoid
If only the latest and greatest will do, the Samsung Galaxy S26 Ultra is the phone for you. It houses the most powerful processor Samsung has ever put in a phone — that's the Qualcomm Snapdragon 8 Elite Gen 5 for Galaxy processor — with even more customization and optimization. The chip is tailor-made for on-device AI tasks and has improved image-signal processing to provide better camera performance. However, the magic really lies within the display.
Literally, the Galaxy S26 Ultra uses Samsung's new "Flex Magic Pixel OLED" technology to deliver a Privacy Display feature. The 6.9-inch screen can limit off-axis viewing with the press of a button by individually disabling wide-angle pixels separate from narrow pixels. This keeps your screen's content completely private.
It's a 120Hz, variable refresh rate panel with QHD+ resolution and inbuilt S Pen support. There's also a new, 200MP primary camera and 50MP telephoto camera with wider apertures for your photography needs. Plus, the rounded corners ensure that your palms won't get uncomfortably poked while holding this big, beautiful phone.
Of course, the Galaxy S26 Ultra is a massive phone with a price tag just as big, so read on if you're looking for something different. On the other hand, it's the only Galaxy S26 model to stay at the same price as its predecessor, so that counts for something.
Best flagship

Specifications
Reasons to buy
Reasons to avoid
Some people want all the bells and whistles, but a lot of people just want a phone that works great and will last a long time without slowing down. That's where the Samsung Galaxy S26 comes in. I recommend it as the more sensible option for people who want a great flagship phone that's both smaller and cheaper than the Ultra variant. Compared to the Galaxy S25, the newer model offers a faster processor, a larger battery, and a bigger screen — plus 256GB of base storage.
The phone is powered by the Qualcomm Snapdragon 8 Elite Gen 5 for Galaxy chipset, comes with new Galaxy AI tools, and features a seven-year OS upgrade guarantee. The 12GB of onboard memory and 4,300mAh battery capacity makes the Galaxy S26 a more complete package than its predecessor. You'll have to pay more for it than the Galaxy S25, though.
Aside from the larger 6.3-inch screen size, the AMOLED display is similar to the Galaxy S25, with a 120Hz variable refresh rate. You don't get the Privacy Display feature from the Galaxy S26 Ultra, which is expected due to the price point. We would've liked to see more camera upgrades, as the Galaxy S26 is still rocking the same setup as the Galaxy S22.
That said, the Galaxy S26's calling card is still the lightweight and relatively thin form factor. It's one of the best compact flagships on the market, if not the best.
Best foldable
Specifications
Reasons to buy
Reasons to avoid
While we're typically more inclined to recommend a Motorola Razr as the best flip phone, the Samsung Galaxy Z Flip 7 takes major steps forward. Samsung's flip phone now features an edge-to-edge cover screen measuring 4.1 inches, and that's actually bigger than Motorola's Razr Ultra 2025. The main display is wider too, making it feel like a Galaxy S26 Plus on the inside. Plus, the new Exynos 2500 chipset is just as good at crushing AI tasks and gaming performance as the competition.
Software has always been a reason to pick a Galaxy Z Flip model over something from Motorola, and it's even better this year. Samsung launched the Galaxy Z Flip 7 with One UI 8, based on Android 16. It became the first Galaxy phone to run One UI 8, alongside the Galaxy Z Fold 7, putting the Galaxy Z Flip 7 ahead of the curve. From there, you'll get seven years of full Android OS upgrades and security updates. That's more than double the amount you'd get with a Razr.
Like its predecessors, the Galaxy Z Flip 7 is water-resistant and is built to withstand the rigors of everyday life, but that also includes protection against larger solid particles. While it's not quite the dust protection we've been asking for, the IP48 rating for the Flip 7 is solid, and Samsung's hinge design and stability are best-in-class.
The list of improvements also includes the Now Bar, Now Brief, and Gemini Live accessible from the cover screen, plus a snappier 120Hz refresh rate. You also get a slimmer and lighter design compared to prior Samsung foldables, making the Galaxy Z Flip 7 easier to stow in a pocket or bag. It's the best Samsung flip phone ever, and it's sure to captivate longtime foldable users and newcomers to the form factor.
Best premium foldable

Specifications
Reasons to buy
Reasons to avoid
The Samsung Galaxy Z Fold 7 is an impressive overhaul that builds on the success of the Galaxy Z Fold 6 Special Edition, released only in China and Korea. Now, the slim and lightweight chassis that model introduced is coming to everyone on the Galaxy Z Fold 7. At only 215 grams, it's actually lighter than the heavyweight Samsung Galaxy S25 Ultra — and only a pound heavier than the Galaxy S26 Ultra. It's not even that much thicker, measuring 8.9mm when closed.
As such, the Galaxy Z Fold 7 is a big foldable you can finally use like a normal smartphone. The cover display is even wider this year, making the outer screen easier to type on and use for quick tasks. The inside is a stunning 8-inch AMOLED panel with a crease that's harder to see than ever before. We lost S Pen support for the sake of thickness, but I think it was worth it.
While the battery size is the same as the Z Fold 6, the battery life is still pretty good. Power users who utilize the main screen all the time might need to recharge to get through a full day, but battery life is still solid for moderate users. There's now a new Qualcomm Snapdragon 8 Elite for Galaxy chip that brings impressive performance to Samsung's best foldable.
We wish Samsung would have improved the charging speeds, though, as it's still stuck at 25W while competitors like the OnePlus Open charge three times faster. There's also no magnets for Qi2 support, which is a bummer as the Google Pixel 10 Pro Fold is launching soon with that feature.
Paired with a new 200MP main camera sensor, the Galaxy Z Fold 7 is Samsung's most complete foldable ever. It should last for years to come with IP48 certification for durability and seven years of Android OS upgrades.
Best mid-range Galaxy

5. Samsung Galaxy A57
Our expert review:
Specifications
Reasons to buy
Reasons to avoid
Like the Galaxy A56 before it, the Samsung Galaxy A57 continues the legacy of the top-tier A-series mid-range smartphones, bringing you great cameras, outstanding battery life, and expandable storage in a phone that costs around $500. Pricing has gone up a bit but compared to the Galaxy A56, you get a much slimmer and lighter phone, faster processor, improved water proofing, and Bluetooth 6.0.
The 2026 refresh get a new Exynos 1680 SoC, which has enabled the use of more Galaxy AI features. The rest of the specs are similar to what the Galaxy A56 offered. The Galaxy A57 starts at $550 and gets you a 5,000mAh battery with 45W charging. Thankfully, there's 8GB RAM as standard for the base variant. You still get three rear cameras which are 50MP, 12MP, and 5MP sensors. The addition of IP68 rating is a big step up. One UI 8.5 ships with the phone, based on Android 16, and there's six year's of OS upgrades promised.
Best budget Galaxy

Specifications
Reasons to buy
Reasons to avoid
The Galaxy A17 isn't Samsung's cheapest Galaxy phone, but it isn't far off. Even so, it gets better update support than some flagships with Android 15 out of the box and six years of software updates promised. It has a 6.7-inch AMOLED display with a 90Hz refresh which looks nice, and Samsung is using the same Exynos 1330 chip which was present in some versions of the A16.
The camera system is decent for this level of phone with the ability to snap some solid pictures in good lighting thanks to the 50MP main sensor. You can take photos all day with the large 5000mAh battery, and storage can be expanded with a microSD card. Samsung ditched the 3.5mm jack this time around, which is a huge shame, but at least there are some dirt-cheap (and really good) wireless earbuds available these days.
This phone supports 5G and if you get the version made for the U.S., it will work on just about any carrier. Other than being slimmer and lighter than the A16, the Galaxy A17 is not too different than its predecessor.
How to choose
Get the right specs
Why you can trust Android Central

Samsung phones are updated every year, and while long-term software support and quality hardware means you don't need to upgrade your phone annually, there are often worthwhile upgrades to entice you to pass on your old one and grab something new. Samsung has even started giving its mid-range phones like the Galaxy S25 FE, seven years of Android upgrades.
As of now, the Galaxy S26 Ultra is the best Samsung phone of 2026, primarily due to its sophisticated blend of super-powered hardware and impressive software features. The 120Hz AMOLED display is sublime, the internal hardware is the fastest of any phone today, and the 200MP camera outclasses most other sensors without trying.
Premium specs often come at a premium price, so the S26 Ultra may not be the best choice for everyone. If you're working with a smaller budget, the base model Galaxy S26 is almost just as good. The S26 boasts a vibrant 120Hz screen with a compact 6.3-inch construction, while the Snapdragon 8 Elite Gen 5 for Galaxy processor — when paired with the 4,400mAh battery — makes the phone run smoother and more efficiently than any base model Galaxy phone to date.
On the more affordable end, Samsung offers the Galaxy A57 5G with hints of the flagship Galaxy S models trickled down to a mid-range price that can be incredibly appealing if you can't push your budget as high as the S26 models. The Galaxy A57 finally gets 8GB RAM as standard, has a 120Hz AMOLED screen, 5G connectivity, and comes with a promise of six Android OS upgrades.
If you're into the flip and foldable style phones, the Samsung Galaxy Z Flip 7 and Galaxy Z Fold 7 cost more but will be conversation starters. Please, they're all just downright cool.
Should you buy the Samsung Galaxy Z TriFold?

The Samsung Galaxy Z TriFold is official, and it's a gigantic folding phone that costs $2,900 in the U.S. The phone is officially available and sold out within minutes of becoming available in the country. Samsung's Galaxy Z TriFold packs a 6.5-inch cover screen and a 10-inch main screen that feels like a full-sized tablet when unfolded. However, the high price tag makes it reserved for the earliest of adopters and power users with the most demanding workflows.
Android Central went hands-on with the Galaxy Z TriFold, identifying the reasons you should (and shouldn't) buy one.
Should you pick a Samsung over an iPhone?

When you compare a Samsung Galaxy phone to an Apple iPhone, we think there's no real contest. While Apple's products have plenty of positive traits — including great customer service at physical Apple Stores — Samsung's phones are feature-rich and often feel a step ahead in terms of technology.
From a physical design standpoint, Samsung phones usually sport bigger screens with smaller bezels around the edges, sleek designs, and sometimes even extra special features like the S Pen built into phones like the Galaxy S26 Ultra. Samsung's displays are world-class and are the brightest you'll find in any phone. There's a reason even Apple uses Samsung displays in its phones.
On top of that, Samsung has been leading the pack in innovation, with devices like the Galaxy Z Fold 7 and Galaxy Z Flip 7, which offer large and impressive foldable glass displays in pocket-friendly form factors.
On the software front, Samsung offers great long-term support for its flagship Galaxy S phones, affordable Galaxy A phones, and its folding phones. The flagships get seven years of support while the more affordable models still get a very competitive four years. We're talking years of support, and optional add-ons like Samsung Care+ are often better than insurance offered through your carrier of choice. Plus, Samsung's AI features keep getting better and are trickling down to lower models too.
Samsung phones ship with a bevy of options that cater to every kind of user, from beginners to power users. And optional downloads like Samsung Good Lock offer customization options that Apple users could only dream of, including plenty of features that most other Android phones don't offer either.
Samsung phones are powered by Android — that's the world's most popular operating system if you didn't know — which means they are compatible with a dizzying array of great accessories and smart products in every category imaginable. Since most smartphones are powered by Android, you could always pick a different non-Apple brand of phone the next time you upgrade and you won't lose access to apps or services you already enjoy on Samsung phones.
Do Samsung phones come with a charger?

Most Samsung phones do not come with chargers these days. Samsung has been making the decision to ship without chargers on a piecemeal basis, typically foregoing them in an effort to become more environmentally friendly and avoid adding e-waste to landfills, as the company previously stated.
Unfortunately, the lack of a charger in the box doesn't mean phone prices have dropped at all. Samsung — and a number of other companies — say that users continue to re-use old chargers and often don't even take new chargers out of the box. Other users pick up great wireless chargers to use in place of traditional wired chargers.
Most premium Samsung phones use 45W charging, further negating the need for a new charger to be included in the box. Samsung finally introduced 60W charging with the S26 Ultra and I'm sure we'll see more models using it going forward. Chance is, if you've got a charger at home already, it's probably no better than a new one that would be included in the box anyway. Thanks to USB-C, however, chances are you have dozens of them lying around that can power Samsung phones.
Do Samsung phones support microSD cards?

SD card support is one of the many casualties of modern smartphone design. Along with 3.5mm headphone jacks, IR blasters, and removable batteries, SD cards have become less and less common. No Samsung flagship phone in 2025 — that means phones that normally cost $800 or more — supports removable SD card storage.
While there could be many legitimate reasons for removing SD card support, two of the biggest are the inclusion of more internal storage and the proliferation of cloud storage. Services like Google Photos can automatically back up your photos and videos, keeping your internal storage free for other apps and games, and many phones ship with at least 128GB of internal storage these days.
But one of the many bright sides of saving a bit of cash on a phone is that, more often than not, budget-friendly phones include budget-friendly features like a 3.5mm headphone jack and removable SD card support. That includes many of the Galaxy A series, like the Galaxy A15, A25, and A35. This means you won't need to spend a bunch of money on expensive internal storage when the best microSD cards only cost a few bucks.
Do Samsung phones support eSIM?

Most modern Samsung phones support eSIM but don't do away with the SIM card tray. That means, on phones like the Galaxy S26, Z Flip 7, Z Fold 7, and even some Galaxy A-series support eSIM.
There are many advantages of having the option to use both eSIM and a physical SIM at the same time. Folks who travel a lot can use multiple carriers that offer better pricing or cell services in different locations. If you have no desire to juggle between more than one carrier, using the same carrier for both eSIM and a physical SIM can increase network bandwidth, offering a way for power users to get better upload and download speeds without having to do much at all.
As usual, the best part of a Samsung phone is the choices offered to users. It's something for everyone!
Get the latest news from Android Central, your trusted companion in the world of Android

Harish Jonnalagadda is Android Central's Senior Editor overseeing mobile coverage. In his current role, he leads the site's coverage of Chinese phone brands, networking products, and AV gear. He has been testing phones for over a decade, and has extensive experience in mobile hardware and the global semiconductor industry. Contact him on Twitter at @chunkynerd.
- Michael L HicksSenior Editor, Wearables & AR/VR
- Roydon CerejoContributor
- Brady SnyderContributor
- Namerah Saud FatmiSenior Editor — Accessories
