How to properly secure your Android phone

Get the latest news from Android Central, your trusted companion in the world of Android
You are now subscribed
Your newsletter sign-up was successful
Google, Apple, and Microsoft have great tools for managing your online security. Some implementations may be technically better than others, but you can be reasonably sure that your data — both on the phone and in the cloud — is safe. If you need more reassurance or have different needs, third-party companies are available that work with the big three to provide enterprise-grade security assurances. No method is 100% secure, and ways to get around it are found regularly, then patched quickly so the cycle can repeat. But these methods are usually complicated and very time-consuming and rarely widespread.
This means you are the weakest link in any chain of security. If you want to keep your data — or your company's — secured, you need to force someone to use these complicated, time-consuming methods if they wanted to get into your phone. Secure data needs to be difficult to obtain and difficult to decipher if someone does get ahold of it. With Android, there are several things you can do to make someone have to work really hard to get your data — hopefully so hard that they don't bother trying.
Use a secure lock screen
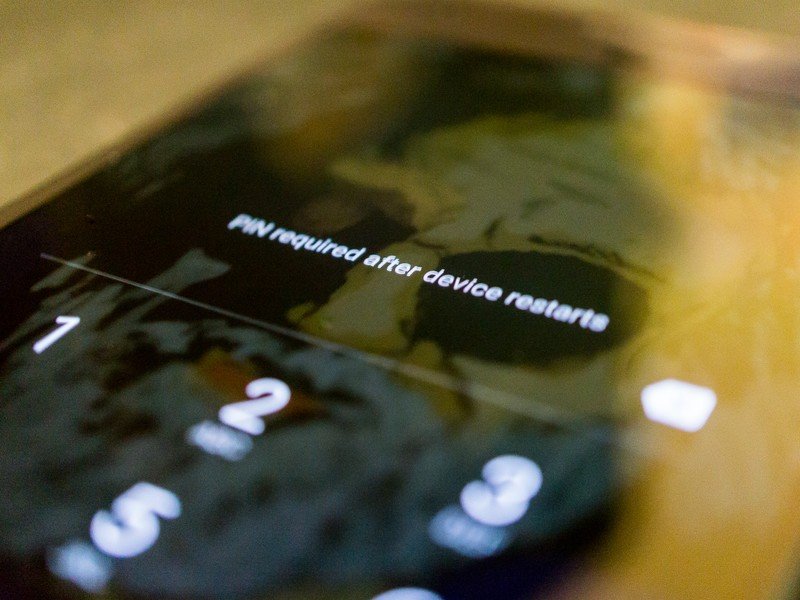
Having a secure lock screen is the easiest way to limit access to the data on your phone or the cloud. Whether you just left your phone on your desk while you had to walk away for a moment or two or if you've lost your phone or had it stolen, a lock screen that isn't simple to bypass is the best way to limit that access.
Article continues belowThe first step is to lock the front door.
If your company issued you a phone or you work for someone with a BYOD policy, there's a good chance your phone is forced by a security policy to have password protection, and your IT department may have assigned you a username and password to unlock it.
Any method that locks your phone is better than none, but generally, a random six-digit PIN is enough to require someone to have special knowledge and tools to bypass it without triggering any self-destruct settings. Longer, randomized alpha-numeric passwords mean they will need the right tools and a lot of time. Entering a long complex password on a phone is inconvenient for you and we tend not to use things that inconvenience us so alternatives have been thought up that use patterns, pictures, voiceprints, and a host of other things easier to do than typing a long password. Read the instructions and overview for each and decide which works best for you. Just make sure you're using one.
Encryption and two-factor authentication
Encrypt all of your local data and protect your data in the cloud with two-factor authentication on your account logins.
Recent versions of Android come encrypted by default. Android 7 uses file-level encryption for faster access and granular control. Your corporate data may have another level of security to reinforce this. Don't do anything to try and lessen it. A phone that needs to be unlocked to decrypt the data is one that only someone dedicated is going to try to crack.
Get the latest news from Android Central, your trusted companion in the world of Android
Online accounts all need to use a strong password and two-factor authentication if offered. Don't use the same password across multiple sites and use a password manager to keep track of them. A centralized spot with all your account credentials is worth risking if it means you'll actually use good passwords.
More: Two-factor authentication: What you need to know
Know what you're tapping on
Never open a link or message from someone you don't know. Let those people email you if they need to make the first contact, and offer them the same courtesy and use email instead of a DM or a text message to get in touch with them the first time. And never click a random web link from someone you don't trust. I trust the Wall Street Journal's Twitter account, so I'll click obscured Twitter links. But I won't for someone I don't trust as much.
Trust is a major part of security at every level.
The reason isn't paranoia. Malformed videos were able to cause an Android phone to freeze up and had the potential to allow elevated permissions to your file system where a script could silently install malware. A JPG or PDF file was shown to do the same on the iPhone. Both instances were quickly patched, but it's certain that another similar exploit will be found, especially when we see stories of flaws like Meltdown and Spectre affecting all our digital things. Files sent through email will have been scanned and links in the email body are easy to spot. The same can't be said for a text message or a Facebook DM.
Only install trusted applications

For most, that means Google Play. If an app or link directs you to install it from somewhere else, decline until you know more. This means you won't need to enable the "unknown sources" setting required to install apps that didn't originate from a Google server in the Play Store. Only installing apps from the Play Store means Google is monitoring their behavior, not you. They are better at it than we are.
If you need to install apps from another source you need to make sure you trust the source itself. Actual malware that probes and exploits the software on your phone can only happen if you approved the installation. And as soon as you're finished installing or updating an app this way, turn the Unknown sources setting back off as a way to combat trickery and social engineering to get you to install an app manually.
With Android Oreo, Google has made it easier to grant trust to a source so you won't have to flip any switches or toggles after you've set things up. This is something Google is always working on because they put their name on the back of every phone and look bad when stories about malware on Android happen.
More: Everything you need to know about the Unknown Source setting
None of this will make your phone 100% secure. 100% security isn't the goal here and never is. The key is to make any data that's valuable to someone else difficult to get. The higher the level of difficulty, the more valuable the data has to be in order to make getting it worthwhile.
Some data is more valuable than others, but all of it is worth protecting.
Pictures of my dogs or maps to the best trout streams in the Blue Ridge Mountains won't require the same level of protection because they aren't of value to anyone but me. Quarterly reports or customer data stored in your corporate email may be worth the trouble to get and need extra layers.
Luckily, even low-value data is easy to keep secure using the tools provided and these few tips.
Updated January 2018: In light of the recent round of web security issues, we have refreshed this page with up-to-date information.

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.
