Meltdown Hack and Spectre Bug: How it affects Android & Chrome Users
You might have heard that the sky has fallen and the security apocalypse has happened because of two new attacks named Meltdown and Spectre. If you work in IT or any other area of large-scale computer infrastructure, you probably feel like it has, too, and are already looking forward to your 2018 vacation days.
Media outlets first heard rumors of this mother-of-all-exploits in late 2017, and recent reports were wildly speculative and finally forced companies like Microsoft, Amazon, and Google (whose Project Zero team discovered the whole thing) to respond with details. Those details have made for an interesting read if you're interested in this sort of thing.
But for everyone else, no matter what phone or computer you use, a lot of what you're reading or hearing might sound like it's in a different language. That's because it is, and unless you're fluent in cyber-geek-security-techno-speak you might have to run it through a translator of some sort.
Good news! You found that translator, and here's what you need to know about Meltdown and Spectre, and what you need to do about it.
What they are
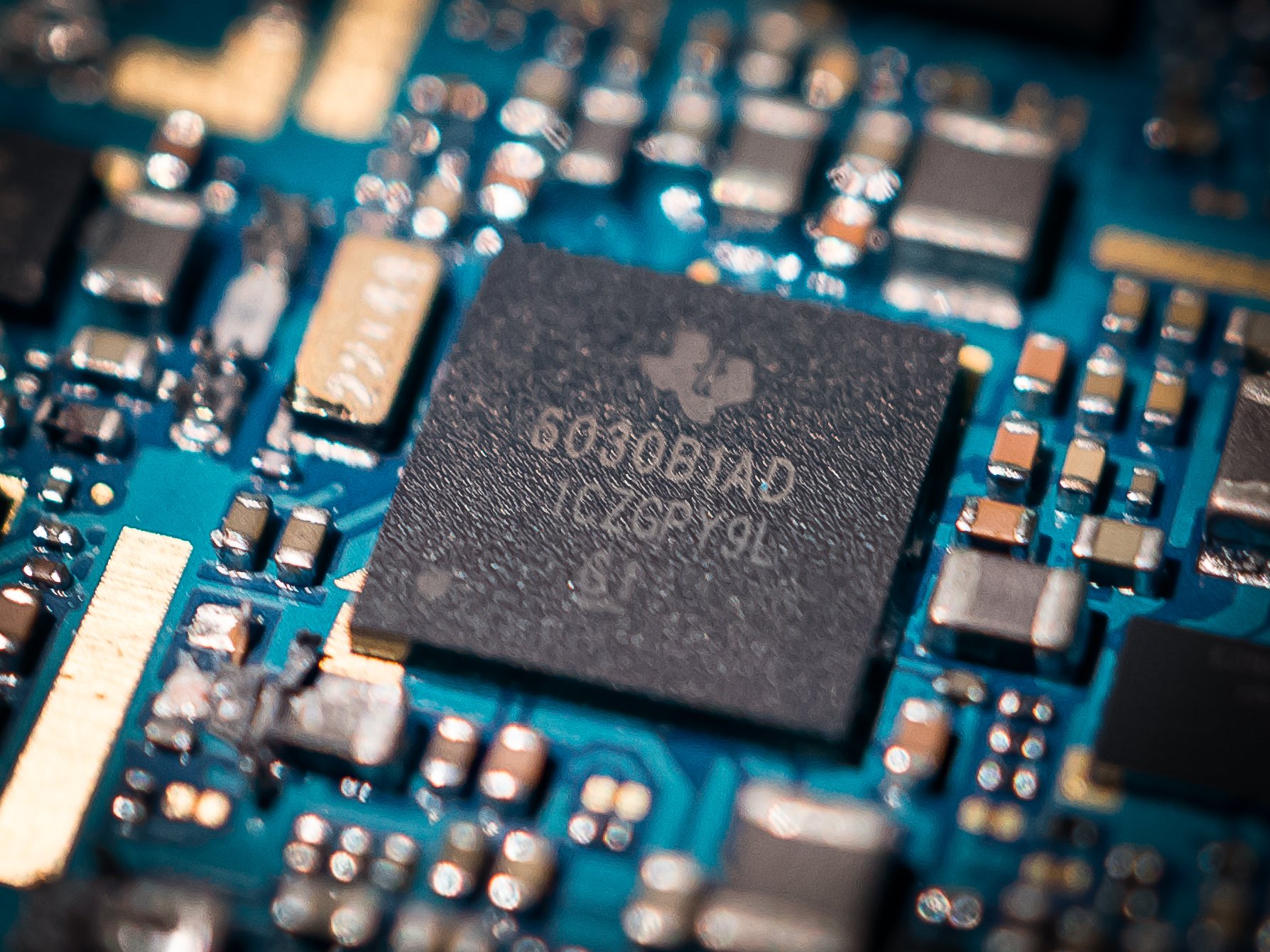
Meltdown and Spectre are two different things, but since they were revealed at the same time and both deal with microprocessor architecture at the hardware level, they are being talked about together. The phone you're using right now is almost certainly affected by the Spectre exploit, but nobody has found a way to use it — yet.
The processor inside your phone determines how vulnerable it is to these types of exploits, but it's safer to assume that they all affect you if you're unsure. And since they aren't exploiting a bug and instead are using a process that's supposed to happen, there's no easy fix without a software update.
Look at the phone in your hands; it's vulnerable to some of these attacks.
Computers (this includes phones and other tiny computers, too) rely on what's called memory isolation for security between applications. Not the memory that is used to store data over the long term, but the memory used by hardware and software while everything is working in real time. Processes store data separately from other processes, so no other process knows where or when it gets written or read.
Get the latest news from Android Central, your trusted companion in the world of Android
The apps and services running on your phone all want the processor to do some work and are constantly giving it a list of things they need to be computed. The processor doesn't do these tasks in the order they are received — that would mean some parts of the CPU are idle and waiting for other parts to finish, so step two could be done after step one is finished. Instead, the processor can move ahead to step three or step four and do them ahead of time. This is called out-of-order-execution and all modern CPUs work this way.
Meltdown and Spectre aren't exploiting a bug — they attack the way a processor computes data.
Because a CPU is faster than any software could be, it also does a bit of guessing. Speculative execution is when the CPU performs a calculation it wasn't yet asked to do based on previous calculations it was asked to perform. Part of optimizing software for better CPU performance is following a few rules and instructions. This means most of the time there is a normal workflow that will be followed and a CPU can skip ahead to have data ready when software asks for it. And because they are so fast, if the data wasn't needed after all, it gets tossed aside. This is still faster than waiting for the request to perform a calculation.
This speculative execution is what allows both Meltdown and Spectre to access data they would otherwise not be able to get at, though they do it in different ways.
Meltdown
Intel processors, Apple's newer A series processors, and other ARM SoCs using the new A75 core (for now that's just the Qualcomm Snapdragon 845) are vulnerable to the Meltdown exploit.
Meltdown leverages what's called a "privilege escalation flaw" that gives an application access to kernel memory. This means any code that can get access to this area of memory — where the communication between the kernel and the CPU happens — essentially has access to everything it needs to execute any code on the system. When you can run any code, you have access to all data.
Spectre
Spectre affects almost every modern processor, including the one on your phone.
Spectre doesn't need to find a way to execute code on your computer because it can "trick" the processor into executing instructions for it, then granting access to the data from other applications. This means an exploit could see what other apps are doing and read the data they have stored. The way a CPU processes instructions out of order in branches are where Spectre attacks.
Both Meltdown and Spectre are able to expose data that should be sandboxed. They do this at the hardware level, so your operating system doesn't make you immune — Apple, Google, Microsoft, and all sorts of open-source Unix and Linux operating systems are equally affected.
Because of a technique that is known as dynamic scheduling that allows data to be read as it's computing instead of it needing to be stored first, there is plenty of sensitive information in RAM for an attack to read. If you're interested in this sort of thing, the whitepapers published by the Graz University of Technology are fascinating reads. But you don't need to read or understand them to protect yourself.
Am I affected?

Yes. At least, you were. Basically, everyone was affected until companies started patching their software against these attacks.
The software that needs updating is in the operating system, so that means you need a patch from Apple, Google, or Microsoft. (If you use a computer that runs Linux and aren't into infosec, you've got the patch already, too. Use your software updater to install it or ask a friend who is into infosec to walk you through updating your kernel). The awesome news is that Apple, Google, and Microsoft have patches either already deployed or on their way in the immediate future for supported versions.
The specifics
- Intel processors since 1995 except for the Itanium and pre-2013 ATOM platform are affected by both Meltdown and Spectre.
- All modern AMD processors are affected by the Spectre attack. AMD PRO and AMD FX (the AMD 9600 R7 and AMD FX-8320 were used as proof-of-concept) CPUs in a non-standard configuration (kernel BPF JIT enabled) are affected by Meltdown. It's expected that a similar attack against side-channel memory reading is possible against all 64-bit CPUs including AMD processors.
- ARM processors with Cortex R7, R8, A8, A9, A15, A17, A57, A72, A73, and A75 cores are suspectable to Spectre attacks. Processors with Cortex A75 (the Snapdragon 845) cores are vulnerable to Meltdown attacks. It's expected that chips using variants of these cores, like Qualcomm's Snapdragon line or Samsung's Exynos line, will also have similar or the same vulnerabilities. Qualcomm is working directly with ARM, and has this statement on the issues:
Qualcomm Technologies, Inc. is aware of the security research on industry-wide processor vulnerabilities that have been reported. Providing technologies that support robust security and privacy is a priority for Qualcomm, and as such, we have been working with Arm and others to assess impact and develop mitigations for our customers. We are actively incorporating and deploying mitigations against the vulnerabilities for our impacted products, and we continue to work to strengthen them as possible. We are in the process of deploying these mitigations to our customers and encourage people to update their devices when patches become available.
- NVIDIA has determined that these exploits (or other similar exploits that may arise) do not affect GPU computing, so their hardware is mostly immune. They will be working with other companies to update device drivers to help mitigate any CPU performance issues, and they are evaluating their ARM-based SoCs (Tegra).
- Webkit, the people behind the browser rendering engine of Safari and the forerunner to Google's Blink engine, have an excellent breakdown of exactly how these attacks can affect their code. Much of it would apply to any interpreter or compiler and it's an amazing read. See how they are working to fix it and keep it from happening the next time.
In plain English, this means that unless you're still using a very old phone, tablet, or computer, you should consider yourself vulnerable without an update to the operating system. Here's what we know so far on that front:
- Google has patched Android against both Spectre and Meltdown attacks with the December 2017 and January 2018 patches.
- Google has patched Chromebooks using the 3.18 and 4.4 versions of the kernel in December 2017 with OS 63. Devices with other versions of the kernel (look here to find yours) will be patched soon. In plain English: The Toshiba Chromebook, the Acer C720, Dell Chromebook 13, and the Chromebook Pixels from 2013 and 2015 (and some names you've probably never heard of) aren't patched yet but will be soon. Most Chromeboxes, Chromebases, and Chromebits are not patched but will be soon.
- For Chrome OS devices that aren't patched, a new security feature called Site Isolation will mitigate any issues from these attacks.
- Microsoft has patched both exploits as of January 2018.
- Apple has patched macOS and iOS against Meltdown starting with the December update. The first round of Spectre updates were pushed out in early January. Check out iMore for everything you need to know about these CPU flaws and how they affect your Mac, iPad, and iPhone.
- Patches have been sent to all supported versions of the Linux kernel, and Operating Systems like Ubuntu or Red Hat can be updated through the software update application.
For Android specifics, the Nexus 5X, Nexus 6P, Pixel, Pixel XL, Pixel 2, and Pixel 2 XL have been patched and you should see an update soon if you haven't already received it. You can also manually update these devices if you like. The Android Open Source project (the code used to build the OS for every Android phone) has also been patched and third-party distributions like LineageOS can be updated.
How to manually update your Pixel or Nexus
Samsung, LG, Motorola, and other Android vendors (companies who make phones and tablets and TVs) will patch their products with the January 2018 update. Some, like the Note 8 or Galaxy S8, will see that before others, but Google has made the patch available for all devices. We expect to see more news from all partners to let us know what to expect and when.
What can I do?
If you have a product that's vulnerable, it's easy to get caught up in the hype, but you shouldn't. Both Spectre and Meltdown don't "just happen" and depend on you installing malware of some sort that leverages them. Following a few safe practices will keep you immune to either exploit on any computer hardware.
- Only install software that you trust from a place you trust. This is a good idea always, but especially if you're waiting for a patch.
- Secure your devices with a good lock screen and encryption. This does more than just keep another person out, as applications can't do anything while your phone is locked without your permission.
- Read and understand the permissions on everything you run or install on your phone. Don't be afraid to ask for help here!
- Use a web browser that blocks malware. We can recommend Chrome or Firefox, and other browsers may also protect you against web-based malware. Ask the people who make and distribute them if you're unsure. The web browser that came with your phone may not be the best option here, especially if you have an older model. Edge and Safari are also trusted for Windows or MacOS and iOS devices.
- Do not open links on social media, in an email, or in any message from someone you do not know. Even if they are from people you know, make sure you trust your web browser before you click or tap. This goes double for redirect links that mask a site URL. We use those sort of links pretty often and chances are a lot of online media you read does, too. Be careful.
- Don't be stupid. You know what this means to you. Trust your judgment and err on the side of caution.
The good news is that the way these side channel exploits are patched is not going to bring the huge slowdowns that were hyped before any updates were released. That's just how the web works, and if you read about how your phone or computer was going to be 30% slower after any fix was applied, it was because sensationalism sells. Users who are running updated software (and have been during testing) just aren't seeing it.
The patch doesn't have the performance impact some claimed it would bring, and that's a great thing.
This all came about because these attacks measure precise time intervals and the initial patches change or disable the precision of some timing sources through software. Less precise means slower when you're computing and the impact was exaggerated to be a lot bigger than it is. Even the slight performance decreases that are a result of the patches are being mitigated by other companies and we see NVIDIA updating the way their GPUs crunch numbers or Mozilla working on the way they calculate data to make it even faster. Your phone won't be any slower on the January 2018 patch and neither will your computer unless it's very old, at least not in any noticeable way.
Stop worrying about it and instead make sure to do everything you can to keep your data safe.
What to take away from it all

Security scares always have some sort of real impact. Nobody has seen any instances of Meltdown or Spectre being used in the wild, and because most devices that we use every day are updated or will be very soon, reports will probably stay this way. But this doesn't mean they should be ignored.
Take security threats like this seriously but don't fall for all the hype; be informed!
These side channel exploits had the potential to be that big, serious game-changing event people worry about when it comes to cybersecurity. Any exploit that affects hardware is serious, and when it attacks something done on purpose instead of a bug it becomes even more serious. Thankfully, researchers and developers were able to catch, contain, and patch Meltdown and Spectre before any widespread use happened.
What's really important here is that you get the right information so you know what to do every time you hear about a new cyberthreat that wants all of your digital stuff. There's usually a rational way to mitigate any serious effects once you dig past all the headlines.
Stay safe!

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.

