NordVPN fesses up to data center breach, insists network is 'still safe'
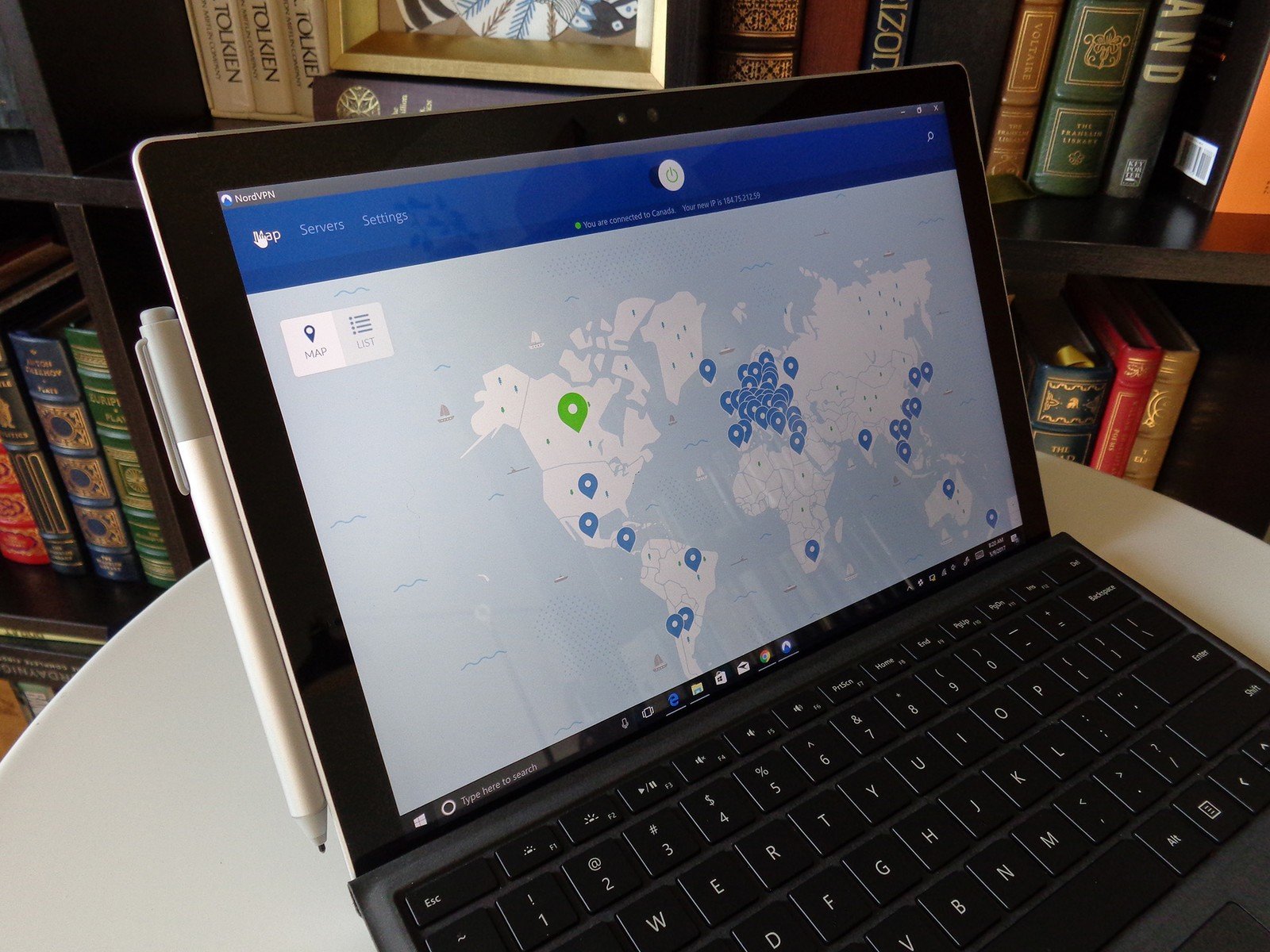
What you need to know
- NordVPN is one of the most popular virtual private network service providers.
- One of its data centers was breached back in March of 2018, the company recently admitted.
- It claims no user activity logs or credentials were compromised.
A Finnish data center hosting NordVPN servers was breached early last year, the company admitted in a blog post earlier today.
It fingered a remote management system used by the data center provider as being responsible for the breach, a system that NordVPN claims it was entirely unaware of. Though it did not name the vendor, the VPN company has terminated its contract with the data center provider and has also shredded all the servers it was renting at the facility.
With regard to activity logs and user credentials, the company insisted that "none of [its] applications send user-created credentials for authentication," so these are secure. The company also makes a big point of its "no logging policy," meaning the former should not exist in the first place.
Alongside this, the company stated that upon its discovery of the breach last year, it immediately commended an extensive audit of its entire network to ensure any other parts of its network were not similarly exposed. That, it explains, was the reason behind the delay in disclosing the breach till now.
However, as researchers cautioned users of the service this week, a (now expired) private security key was also exposed due to the breach, which could allow anyone to set up their own servers disguised as NordVPN.
"However, the key couldn't possibly have been used to decrypt the VPN traffic of any other server. On the same note, the only possible way to abuse website traffic was by performing a personalized and complicated MiTM attack to intercept a single connection that tried to access nordvpn.com," said the company's Daniel Markuson.
To keep its network secure in the future, the company is purportedly moving all of its servers to RAM, something that it says will be completed by next year. It's also launching an application security audit and a no-logs audit, and is preparing a bug bounty program to ensure the continued safety of its network.
Get the latest news from Android Central, your trusted companion in the world of Android
Best VPN apps for Android in 2019
We test and review VPN services in the context of legal recreational uses. For example:
1. Accessing a service from another country (subject to the terms and conditions of that service).
2. Protecting your online security and strengthening your online privacy when abroad.
We do not support or condone the illegal or malicious use of VPN services. Consuming pirated content that is paid-for is neither endorsed nor approved by Future Publishing.