T Mobile
T-Mobile Coverage Map | T-Mobile Website
T-Mobile is a wireless carrier in the U.S. that is currently the fourth-largest in the country by number of subscribers. Known for its token commercial jingle and magenta color scheme, T-Mobile drives itself on the message of being an "Uncarrier" that does things the other carriers just won't do. It's well known as a value-based option to the other three major carriers, with lower prices for data and fewer restrictions on usage than its competitors. Though it is no longer a wholly-owned subsidiary of Germany's Deutsche Telekom, DT now holds a majority of the now-public T-Mobile U.S. stock.
Following a failed attempt to be acquired by AT&T at the end of 2011, T-Mobile gained a huge sum of money and spectrum holdings as part of the deal to the tune of $4 billion. Using this money and a change in leadership at the carrier, T-Mobile quickly turned itself around to start gaining customers and posting small profits for the first time in years. From 2012 to 2014 it launched and rapidly deployed an LTE network, quickly bringing it up to speed in terms of technology and coverage with the other carriers. Part of that expansion came with the purchase of MetroPCS, a smaller regional carrier, which brought in more customers, new spectrum and subsequently made T-Mobile a publicly-held company through the merger.
In terms of network technology, T-Mobile operates a GSM and LTE network across 700MHz, 1900MHz and the combined 1700/2100MHz (also known as AWS) frequencies. During its vast expansion of LTE throughout 2013, T-Mobile shifted its spectrum holdings in a way that better aligned itself with the network map of AT&T, making it easier for customers of that carrier to bring their phones over to T-Mobile without issue. Though it has made huge strides in terms of coverage in recent years, T-Mobile is often dinged — both by customers and competing carriers — for its lack of extensive rural coverage around the country.
Latest about T mobile

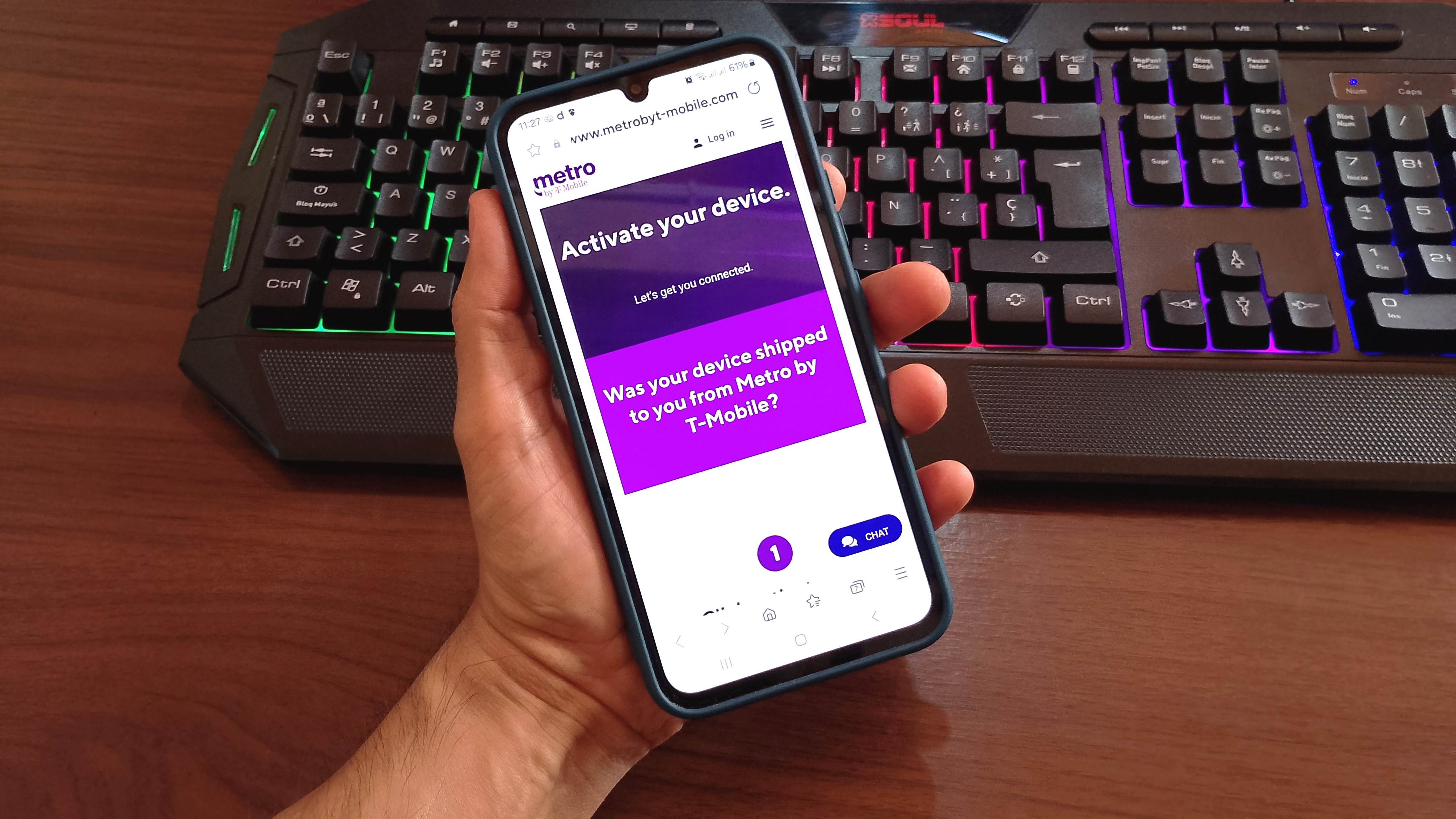
Metro by T-Mobile is slashing 50% off its unlimited plan — score six months for only $20 per month!
By Patrick Farmer published
5G for cheap For a limited time, Metro by T-Mobile will give you six months of its Unlimited 5G Data plan for a single payment of $120.

This is not a test: T-Mobile will already give you the TCL NXTPAPER 70 Pro for FREE with new deal
By Patrick Farmer published
Easy on the eyes This eye-friendly smartphone has already gone viral, and now you can get your own for FREE by adding a line at T-Mobile.

Best wireless plans for international travel 2026
By Patrick Farmer last updated
Travel smart! With one of these best wireless plans for international travel, you can use your phone to its fullest, no matter which country you're traveling to.

Wait no more: TCL's e-paper NXTPAPER 70 Pro is at T-Mobile for cheap
By Nickolas Diaz published
It's like paper TCL confirmed that its NXTPAPER 70 Pro is available at T-Mobile with its paper-like display for eye health at a cheap price point.

T-Mobile will apparently give you a free Pixel phone AND some earbuds this month — here's how to claim yours
By Patrick Farmer published
Get equipped T-Mobile will now give you a free Google Pixel 10a and a pair of Pixel Buds 2a earbuds when you add a line with "most plans" on the carrier's site.

New Mint Mobile deal gets you a full year of 5G internet AND unlimited wireless for only 45 bucks per month — this isn't a joke
By Patrick Farmer published
Bundle savings Mint has launched a bundle deal that gets you a year of 5G Home Internet and T-Mobile-powered wireless for only $45 per month

The best T-Mobile deals of April 2026: Galaxy S26 deals, home internet savings, and more
By Patrick Farmer last updated
Join the party T-Mobile has no shortage of great deals on Android phones; here are some of my favorites from this month.

These 6 prepaid SIM cards for US tourists will take your 2026 travels to the next level
By Patrick Farmer last updated
Travel in comfort With these best prepaid SIM cards for U.S. travelers and tourists, your upcoming visit to the United States will end up being a memorable affair.

The best prepaid phone plans for Android users 2026
By Samuel Contreras, Namerah Saud Fatmi last updated
Go prepaid, save more! With one of the best prepaid phone plans, you can enjoy everything from high-speed 5G connectivity to mobile hotspot data, all at affordable prices.

Last call! Grab a free Samsung Galaxy S26 Ultra from T-Mobile before the deal ends on April 1st
By Patrick Farmer published
Ends April 1st! T-Mobile's viral deal that gets you a free Galaxy S26 Ultra with a new line is set to end on April 1st.

Can you really get a FREE Galaxy S26 Ultra without trade at T-Mobile? Here's what you need to know about the viral deal
By Patrick Farmer published
Pure power Add a line with the Experience Beyond plan and T-Mobile will give you a free Samsung Galaxy S26 Ultra. It's as simple as that.

Best wireless carrier in the U.S. 2026
By Patrick Farmer last updated
Take your pick! Selecting the best wireless carrier for yourself, your family members, and friends doesn't have to be a chore. Here are some feature-laden choices.

Metro by T-Mobile launches deal that gets you six months of unlimited wireless for only $120
By Patrick Farmer published
Huge savings Metro by T-Mobile just launched one of the best wireless deals I've seen all year.

Three ways to get a FREE Samsung Galaxy S26 Ultra before the big release
By Patrick Farmer published
Last chance! T-Mobile, Verizon, and AT&T are all running deals that could get you a free Galaxy S26 Ultra — you just need to meet the eligibility requirements.

Yes, T-Mobile will really give you the Pixel 10a AND some earbuds for free with "most plans" — so what's the catch?
By Patrick Farmer published
Phone + buds = happy Google's cheap phone literally just hit store shelves today, and the carrier deals are already this good.

T-Mobile still wants to give you $300 to try its 5G Home Internet service
By Patrick Farmer last updated
No way! T-Mobile 5G Home Internet will give you $300 to try its All-In plan, plus a five-year price guarantee, streaming subscriptions, and more.

That's not a typo: T-Mobile will really give you a FREE Samsung Galaxy S26 Ultra when you preorder — no trade-in required!
By Patrick Farmer published
Preorder party The Galaxy S26 lineup has finally been revealed, and T-Mobile is already out here with one of the best preorder deals I've seen in ages.

Just a few days before Unpacked, T-Mobile wants to give you the Galaxy S26's biggest competition for FREE (no trade-in required)
By Patrick Farmer published
Pixel perfect We're about to get a first look at the new Samsung lineup, but who cares about brand loyalty when there's a free phone on the line?
Get the latest news from Android Central, your trusted companion in the world of Android