How to update the Trusted Platform Module on your Chromebook
Chromebooks and Chromeboxes are some of the most secure computers currently on the market. They can't run traditional programs, which means that viruses and malware designed for Windows and macOS just don't work. If Chrome OS is modified in any way, the device will flash a scary warning message every time it's turned on. These — combined with an interface that is easy to use — make Chromebooks great computers for almost anyone.
But there are still vulnerabilities to be aware of. Technology isn't magic, and even the most secure systems need regular maintenance. For the most part, this happens automatically — Chromebooks download OS and security updates in the background, and they get installed when a user reboots the machine. Recently, a flaw was discovered with the Trusted Platform Module — or TPM — used in almost every Chromebook.
The TPM is the chip responsible for a whole bunch of stuff — mostly having to do with securely storing really sensitive content like security keys and administrative passwords for your device. The firmware for the TPM is updated separately from the rest of the operating system for extra security.
The TPM maintains its own private keys, but bugs in some TPM versions could make those private keys available to attackers. In practical terms, that could expose device data and allow someone to brute force their way into your account. If you have one of these Chrome devices, you may be running one of the affected TPM versions.
Here's how to find out if you need to complete the update:
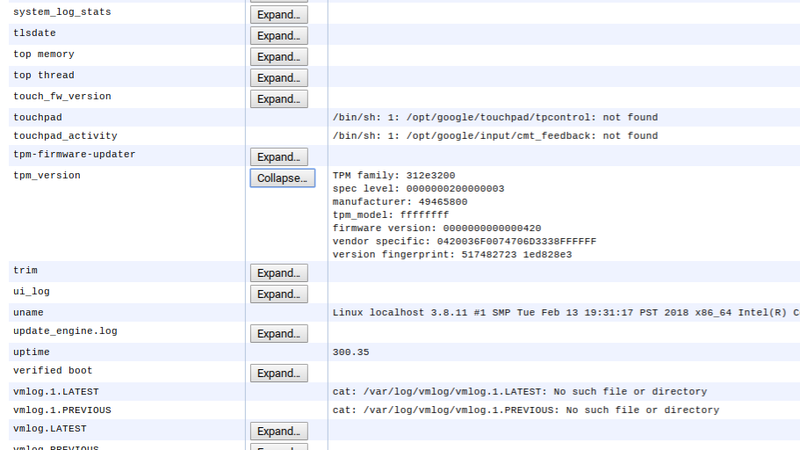
- Type chrome://system in the Chrome search bar.
- This page displays all the hardware and software information about your device, so wait a minute or two for it to all load.
- Press Ctrl + F on your keyboard to open a search box.
- Type tpm. The second result will be tpm_version.
- Click expand next to tpm_version to display your TPM's firmware version.
If you have one of the below firmware versions, you will need to install the update:
- 000000000000041f - 4.31
- 0000000000000420 - 4.32
- 0000000000000628 - 6.40
- 0000000000008520 - 133.32
If you have one of these firmware versions, you are already protected against the bug:
Get the latest news from Android Central, your trusted companion in the world of Android
- 0000000000000422 - 4.34
- 000000000000062b - 6.43
- 0000000000008521 - 133.33
Fortunately, all you have to do to install the update is Powerwash your Chromebook. Unfortunately, this will erase your local data. Be sure to backup any local files you or other users have. When you go to Powerwash your Chromebook, you'll see an extra check box that says "Update firmware for added security". Check this box, let your device reset, and that's it! Just set your Chromebook back up and you're done.
When was the last time you updated your Chromebook? Let us know down below!