Google's Android Security Bulletin for July 2016 has two patch indicators
Welcome to another thrilling episode of Important Things Google Fixed with your host, Android Central! Every month for over a year now, Google has been releasing monthly updates to keep as many Android phones as possible more secure than they were the month before. During that time we've seen some of Google's partners make a real effort to deliver those updates every month, while other fall a little short when it comes to keeping their users safe.
Every month the list of things Google and their partners have discovered and fixed in Android is a little different, but unlike previous patch updates this month there will be two different indicators that your phone is up to date. We've got a quick breakdown of what those two dates are, and what they mean for the security of your phone.
Patch Level — July 1, 2016
In every month but one so far, the patch level on your Android phone has been marked as the first of whatever month that update was released by Google. For many users, this month will not be any different. The July 1 2016 patch this month is a list of Android includes fixes for remote code execution vulnerabilities in the Mediaserver, as well as in OpenSSL and BoringSSL. Google has also fixed 12 different elevation of privilege vulnerabilities across Android, and dealt with Denial of Service vulnerbilities in libc and Mediaserver.
A complete list of the vulnerabilities addressed in this month's patch can be found on the Google Developer Site. Google has not found any evidence to suggest active customer exploits are happening using any of the vulnerabilities that have been fixed in this patch.
Patch Level — July 5, 2016
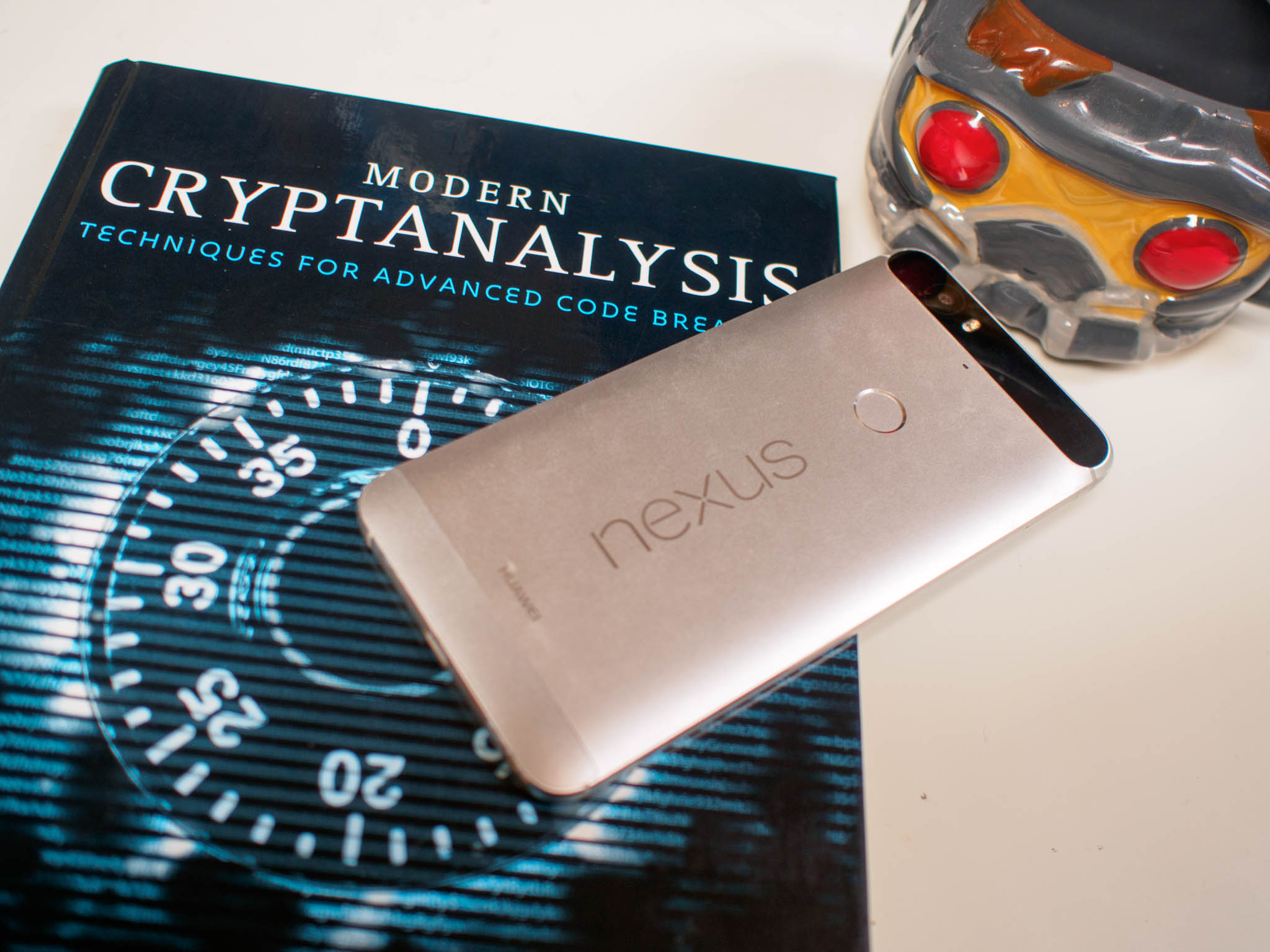
This second patch includes everything you'll find in the July 1 2016 patch, but also includes patches for a great number of drivers in Nexus, Pixel, and Android One hardware. This includes fixes for Qualcomm, Mediatek, and Nvidia drivers that address a significant number of components across Google's hardware lineup. These driver fixes can be applied to non-Nexus hardware, but may require additional work on behalf of the hardware manufacturer to ensure stability with their existing firmware.
A complete list of the vulnerabilities addressed in this month's patch can be found on the Google Developer Site. Google has not found any evidence to suggest active customer exploits are happening using any of the vulnerabilities that have been fixed in this patch. You can head to Google's OTA page for factory images with this patch for your Nexus phone.
What happens if I only have July 1, 2016?
Google's decision to split these two groups of patches out does not necessarily mean that your phone is less secure if you have July 1 instead of July 5.
Get the latest news from Android Central, your trusted companion in the world of Android
Devices that use the July 1, 2016 security patch level must include all issues associated with that security patch level, as well as fixes for all issues reported in previous security bulletins. Devices that use July 1, 2016 security patch level may also include a subset of fixes associated with the July 5, 2016 security patch level.
It's not overly likely we'll see any manufacturer release a July 1 and a July 5 update this month, but Google's decision to split the updates up like this hopefully means more phones will get the much needed July 1 updates with the expectation that the applicable July 5 updates would be applied with the August update. Like all previous updates, Google's were notified of the issues found and fixed in this update 30 days ago. Keep an eye out for which update your phone gets!


