WhatsApp group chat security flaw: What you need to know

A lot of talk went down recently about a new way to exploit WhatsApp and bypass the end-to-end encryption the company likes to mention that it has whenever it can. I've seen tweets and comments that run the gamut from "it's FUD" to talking about some backdoor that Facebook had installed.
The good news is that it's neither. In fact, it's not really one of those things you need to be concerned about and instead is one of those things that make you wonder how it ever happened in the first place because it's pretty sloppy. But don't worry — it will be fixed long before anything happens.
What it is
Researchers Paul Rösler, Christian Mainka, and Jörg Schwenk at Ruhr-Universität in Bochum, Germany released a research paper (.pdf link) that found a peculiar flaw in WhatsApp's group chat administration. WhatsApp offers the same end-to-end encryption for group chats that it does for individual chats, and that usually means we should be able to feel safe in knowing that the things we say won't be read by anyone who shouldn't be reading it unless one of the group members lets it happen.
Apparently, it's theoretically possible for a stranger to add themselves to a group chat on WhatsApp. "Theoretically" and "possible" being the key words here. I'll explain.
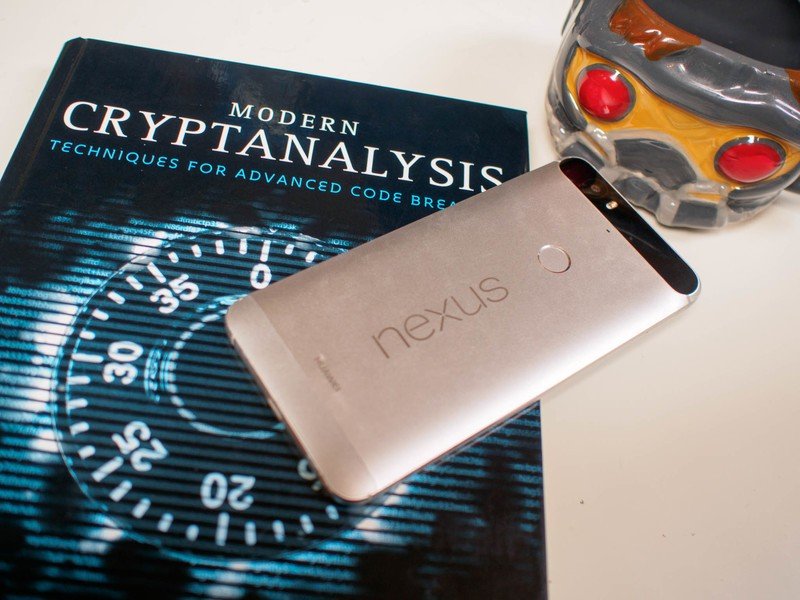
WhatsApp offers group messaging that uses strong end-to-end encryption.
In a WhatsApp group chat one or more of the original members is an administrator. From the server's point of view, that means that these people are able to add and remove people from the group. Everything is good so far, even though the way it works — an administrator sends a signal to every member of the group with his or her signing keys and in return, each member sends a return message with their signing keys then the originator of the message notifies each member that there is now a new person in the group — is a bit of a kludge in order to create a good user interface. If you're not an administrator, the only thing you know is that you see a message that Jerry is now a member of the group. You can either accept that or leave the chat.
A similar flaw was found with group messaging through Signal.
The problem is that WhatsApp isn't properly authenticating these group management requests on its own servers. A WhatsApp server needs to properly ID the sender of a message that would add a person to a group chat. The person sends a message that IDs both the group and the member it wishes to add and the server checks to make sure the person who sent it is actually a chat administrator. These messages aren't end-to-end encrypted, and instead use standard transport encryption — the message coming from a chat administrator and going to a server that requests a user be added to a chat is not signed by the sender with their encryption key.
This means a WhatsApp server can add any user it wants to any group, at any time. The server can, not another user. That's important, and it means any privacy expected in a WhatsApp group chat depends solely on trusting the WhatsApp chat server. That defeats the entire purpose of end-to-end encryption, which is designed so that privacy is guaranteed even if a server is compromised because only the sender and recipient can decrypt a message.
Get the latest news from Android Central, your trusted companion in the world of Android
And then the internet loses its collective mind because that's what the internet is really good at doing.
This won't happen but still needs fixing
The only way this flaw can be exploited is by someone with access to the server doing it. That means a server gets compromised, or an employee goes rogue, or a three-letter government agency files a warrant. Any of those things could happen, might have happened in the past, and could even be happening right now. But one other thing needs to be considered — you'll know if it happens to your chat.
You are notified whenever a person is added to a group chat, encrypted or not.
The first thing that a server does after a member is added is notify every other member of the group that "Jerry was added to the chat." You will see the message telling you someone was added, and so will everyone else. When Jerry arrives to the private chat party with his bad jokes and cheap beer, and nobody invited him, that's going to be a sign that something's wrong and nobody should consider anything they are about to type as private. Pack up and move to another chat without Jerry and maybe even a different service that won't let him crash.
So nobody is going to be able to secretly check out your encrypted group chat, but this still undermines end-to-end encryption in every possible way. It needs to be fixed right away, and maybe even the whole group management method needs to be revamped. At the bare minimum, we all need to scratch our heads and wonder how something like this slips by programmers and code auditors. It's a ridiculous premise that will never be exploited, but still.
What you need to do
Nothing, really. Appreciate the work done by Rösler, Mainka, and Schwenk in finding this flaw because security researching is a thankless and often mind-numbing job, but past that you don't really need to change your routine at all. A method of authenticating the request to add a member to an encrypted group chat will be sorted out by the folks who keep WhatsApp's wheels spinning shortly and this will change from a flaw that will never be exploited to a flaw that can no longer be exploited at all.
What's important is that you were paying attention, because the next flaw might very well be one that does need action on your part. And there will be another flaw, so make sure you keep paying attention.

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.

