Leaked Android certificates left millions of smartphones vulnerable to malware
You should always be wary when you sideload apps to your Android phone.
What you need to know
- It was discovered that crucial Android keys to sign system apps were leaked.
- This could provide bad actors with an easy way to inject malware into Android devices through apps.
- The vulnerability was apparently
A major Android leak left smartphones from Samsung and LG vulnerable to malware, according to a Googler who brought the issue to light.
According to Łukasz Siewierski (via Mishaal Rahman), a Google employee and malware reverse engineer, the certificates of several Android OEMs were leaked, which could have been used to inject malware into smartphones. This vulnerability affected major Android companies, including Samsung, LG, and MediaTek.
Companies like Samsung use platform certificates to validate their apps for use within Android. As described in the issue tracker, apps signed with this certificate run with a "highly privileged user id - android.uid.system - and holds system permissions, including permissions to access user data. Any other application signed with the same certificate can declare that it wants to run with the same user id, giving it the same level of access to the Android operating system."
Basically, apps using these certificates from major OEMs could gain access to system-level permissions without user input. It's especially problematic because bad actors could disguise their apps as system apps with this method. System-level apps have far-reaching permissions and can usually do/see things on your phone that no other app can. In some cases, these apps have more permission than you do.
For example, malware could be injected into something like the Samsung messages app. This could be signed with the Samsung key. It would then appear as an update, pass all security checks during installation, and give malware almost total access to your user data across other apps.
Folks, this is bad. Very, very bad. Hackers and/or malicious insiders have leaked the platform certificates of several vendors. These are used to sign system apps on Android builds, including the "android" app itself. These certs are being used to sign malicious Android apps! https://t.co/lhqZxuxVR9December 1, 2022
There is some good news, as the Android Security Team highlights that OEMs have apparently addressed the issue.
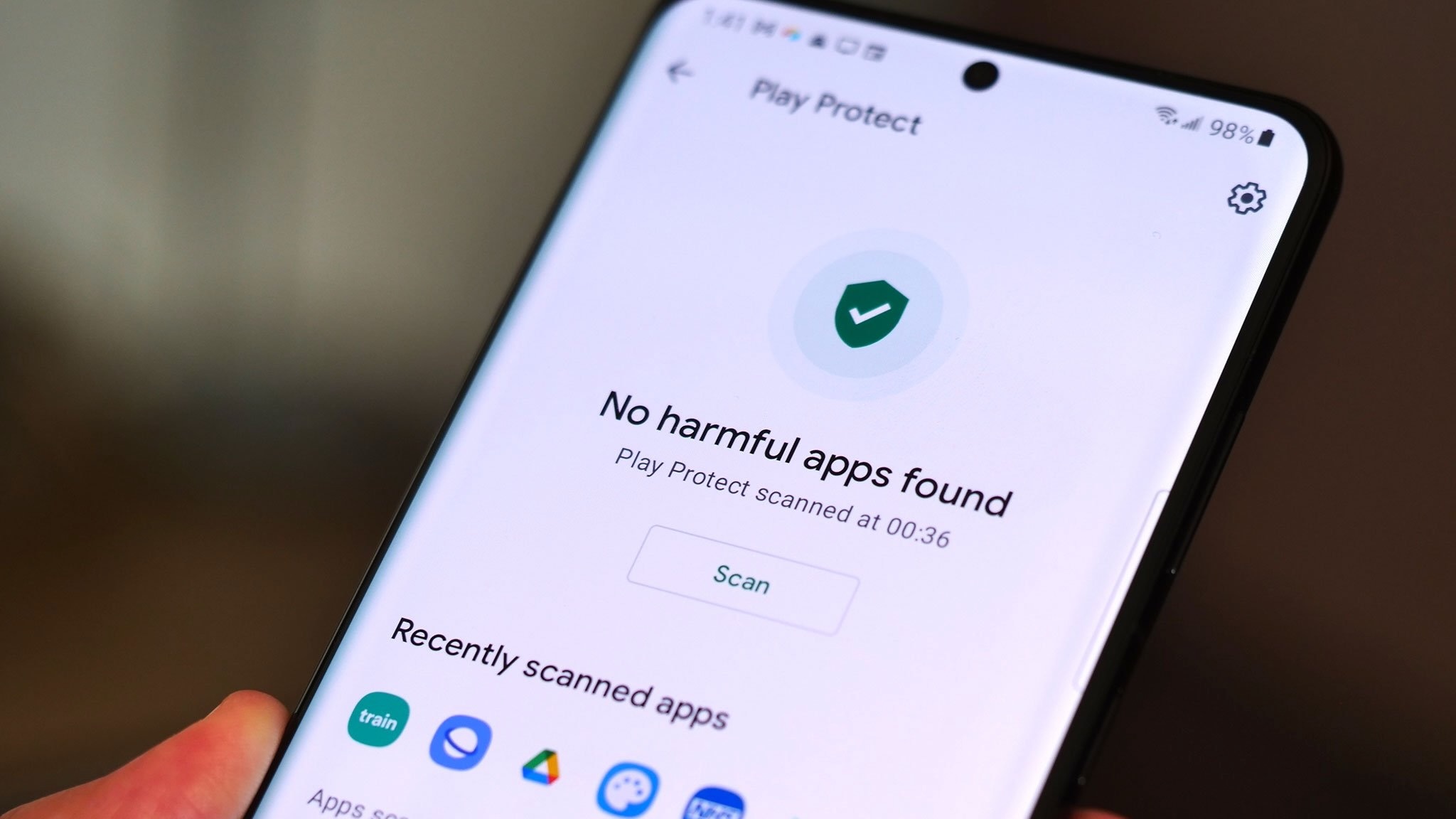
"OEM partners promptly implemented mitigation measures as soon as we reported the key compromise. End users will be protected by user mitigations implemented by OEM partners. Google has implemented broad detections for the malware in Build Test Suite, which scans system images. Google Play Protect also detects the malware. There is no indication that this malware is or was on the Google Play Store. As always, we advise users to ensure they are running the latest version of Android."
Get the latest news from Android Central, your trusted companion in the world of Android
Samsung also told Android Police in a statement that updates have been issued since 2016 and that "there have been no known security incidents regarding this potential vulnerability."
In any case, because of the protections provided by Google Play Protect, users should not have to worry about these vulnerabilities from apps they install from the Play Store. However, you should always be wary of sideloading apps to your Android phone and always ensure you're using the latest version of Android.

Derrek is the managing editor of Android Central, helping to guide the site's editorial content and direction to reach and resonate with readers, old and new, who are just as passionate about tech as we are. He's been obsessed with mobile technology since he was 12, when he discovered the Nokia N90, and his love of flip phones and new form factors continues to this day. As a fitness enthusiast, he has always been curious about the intersection of tech and fitness. When he's not working, he's probably working out.

