A nearly impossible to remove Android malware has infected 45,000 devices

What you need to know
- The app has infected over 45,000 devices in the last six months, says Symantec.
- The malware has, so far, only carried out relatively benign activities such as showing pop-up ads and unwanted notifications.
- The most notable thing about xHelper is its persistence. Even factory resets are no match against it.
A new security threat has been making mobile security researchers scratch their collective heads for the past few months. It's called xHelper, and this is one app that just can't take a hint.
Only about seven months old, the malware had already reached MalwareBytes' top 10 list of malware by August. Symantec, on the other hand, says it has detected at least 45,000 infections by the app thus far, with more every day. Security researchers say the app is being distributed via websites that encourage users to sideload apps onto their device. These apps then install the xHelper trojan onto the device.
After installation, the app then proceeds to spam the device with notifications and pop-up ads. Both Symantec and Malwarebytes note that the app's nefarious activities are seemingly only limited to these prompts encouraging you to download other apps or play online games. That is likely the primary source of revenue for the group behind the app, as each click or install earns them a tiny bit of money.
What's far more interesting is the care that's taken in ensuring the app cannot be removed from the device. Not only does the app prefer to operate silently from the shadows, but it also jumps through various hoops and uses encryption to mask its installation. Detection is the first step in combating malware and the ingeniously crafted malware is meticulous about hiding both its installation and its existence from the user.
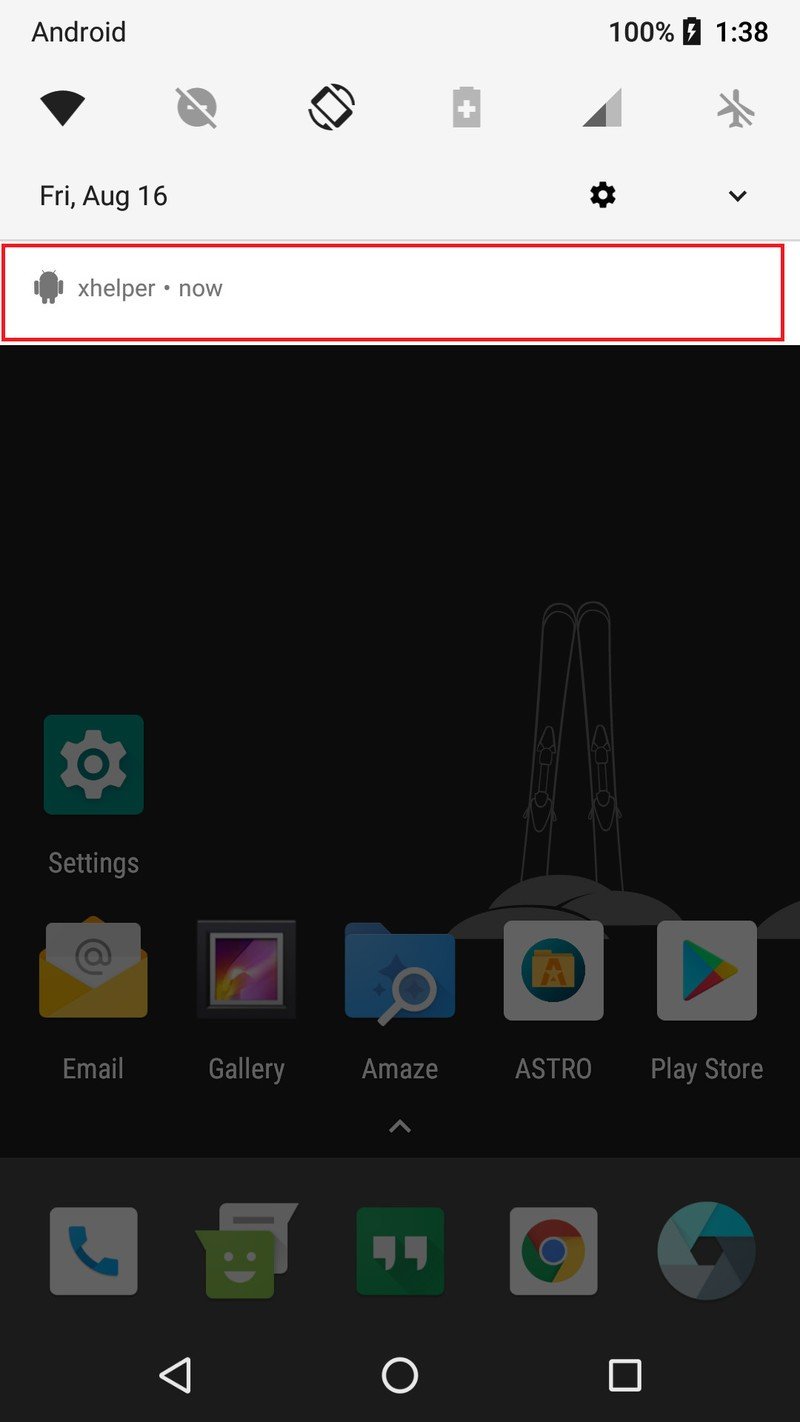
Malwarebytes suggests the app comes in two variants: semi-stealth and full-stealth. In both configurations, the app does not create an app icon or a shortcut icon in order to ensure users do not notice the app's presence on their device. This also prevents them from easily uninstalling the nasty piece of work from their devices; after all, if there's no app icon on your launcher, how can you drag it to the uninstall button? The only way an average smartphone user would even notice its presence is thanks to the xHelper notification icon that these ad notifications are accompanied by in the app's semi-stealth variant. The full-stealth configuration doesn't even have that.
Lacking a launcher icon, xHelper is designed to automatically begin running as a foreground service based on various triggers, such as when the device is booted or the power is connected/disconnected. Once that's done, even if you uninstall the app that xHelper came with, the malware will continue to reside on your device.
Planning on manually stopping the service? xHelper will restart it to ensure it keeps pushing ads at you. You've removed the service altogether? xHelper will magically reappear on your phone. Are you finally enraged enough to consider nuking your phone with a factory reset? Don't bother, because xHelper will inexplicably come back. And that's the most dangerous thing about xHelper: its persistence in always being there to 'help' you to a serving of ads and spam whether you want it or not. Researchers at Symantec have so far been unable to decipher the mechanism through which the app is able to resurrect itself from the dead even after a factory reset.
Get the latest news from Android Central, your trusted companion in the world of Android
In the interest of keeping your device as safe as possible, it's always a good idea to not sideload apps outside the Play Store. Also, be very careful about pages that redirect you to other websites and never click on anything if you have been redirected to an unknown site.
While the app has so far stuck to the mostly 'benign' realm of serving unwanted ads, Symantec's researchers note that the service also establishes connections to a remote server for the purpose of receiving commands. This could easily allow the malware to go from an unwanted nuisance to a significant security threat capable of installing other malicious applications on the device or even hijacking the phone entirely. That capability, combined with its legendary persistence, makes xHelper one terrific threat in the mobile realm.


