Google Play services bringing new OAuth tools to Android
Google is rolling out Google Play services starting today, bringing another of the great developer tools they showcased at Google I/O to the public.
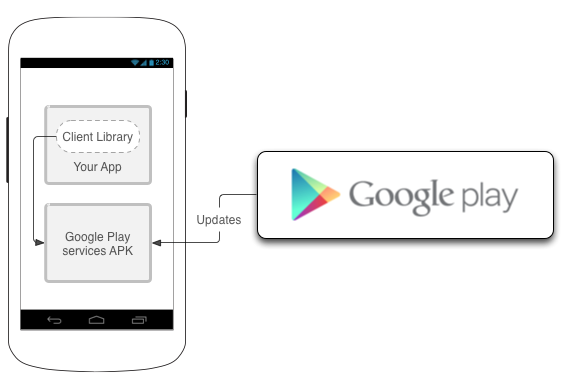
For those of us that aren't developers, it's pretty easy to wrap your head around. If your device runs Froyo or higher and has access to the Google Play store, you'll have a new Google component to download. It's a set of libraries and tools that developers can use to authenticate with your Google account. When an app needs to access your private data from a Google application, they can use the new tool to get that access securely without requiring you to enter the (hopefully) long and secure password you use for your Google account. Version one of the service includes Google+ sign-in and +1 APIs as well as new OAuth 2.0 functionality.
OAuth 2.0 is a pretty big deal. It scales better than previous versions, is more secure, and as Googler Tim Bray notes "especially, because typing your password into a mobile device sucks". Bray has also posted an excellent overview, complete with code samples, using the new OAuth components at the Android Developers blog.
Best of all, this will all be transparent to the end user. Once the required code is installed on your Android phone or tablet, the rest is up to developers. No more typing in your password on a mobile webpage, or getting a one-time password from Google two-step verification, we'll simply be able to choose the account we would like to use and go. We see that now with many of Google's apps, but the new method will bring it all together for a consistent -- and safe -- user experience using open standards.
The developer portion of the service is available now, and you can find all the info you need to start using it at the links below. The client side (what we'll need on out phones) should be rolled out completely in the coming weeks, and we'll start seeing apps use the service once Google announces the rollout is complete.
Source: +Android Developers; More: Android Developers blog, Google Developers, Tim Bray
Get the latest news from Android Central, your trusted companion in the world of Android

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.

