Chrome browser will soon mark all HTTP pages as 'Not secure', because they aren't
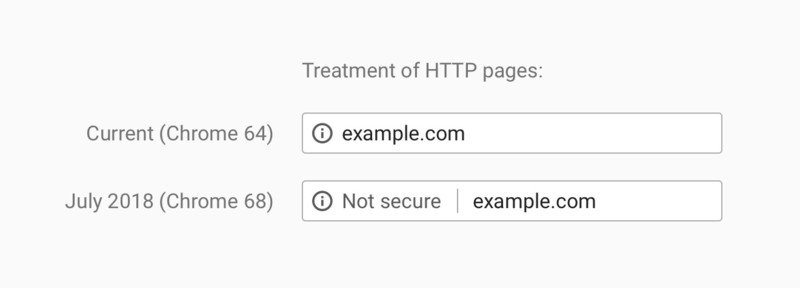
Google wants to rid the web of sites not protected by HTTPS encryption, and it has told us how it is going to do its part to let everyone know that "regular" HTTP sites are "Not secure" in Chrome version 68.
Coming in July 2018, whenever a user navigates to an HTTP site in Chrome the Omnibox will spell it all out.
It's important to remember that this won't actually affect the loading of an HTTP web site, but will only serve as a notice for users. Google has been selectively marking HTTP pages as not secure for about a year any time a Chrome user enters any data on a page and for every HTTP page visited when using Incognito mode. Today's news just means that it's going to happen to every site, for every user with Chrome 68 for Android, iOS, Windows, Mac, and Linux as well as Chrome OS version 68.
HTTPS uses certificates and encryption layers to keep private data between you and the website you want to have it.
HTTPS is short for HyperText Transfer Protocol Secure and it means that the connection between you and a website is happening on secure channels. Trust certificates are used as a way to encode and decode encryption, and unless a certificate vendor (like Verisign) fouls up nobody but you and the website can read the data you're sending. Thankfully, that doesn't happen very often, which makes it the best way to stay secure without shaking up the way the internet works and how browsers send and read user data.
Google also has beefed up its developer tools in order to help developers make the move, most notably the Lighthouse automated tool which can check what's ready and what's not for even the most complicated domain. Interested web devs can check out some handy set-up guides to get started.
Like any business, Google has to look after its own interests first. it's great when their interests line up so well with what's best for everyone.
Get the latest news from Android Central, your trusted companion in the world of Android

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.

