More Android Market security woes -- and a novel idea to fix them from Sophos
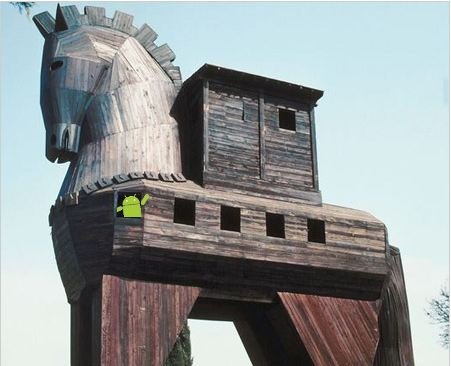
Malicious files once again have found their way into the Android Market, with a set of applications being hijacked, reverse engineered with malicious code injected, and published alongside the legitimate applications.
Two thing need mention up front -- Google has already removed the apps from the Market, and this time around they only affected users in China, where they also originate from. If you're reading this story, you probably are safe and never were at risk. But this is still a big concern. A set of bad guys (that's my safe-for-work version) were able to de-compile apps from a legit developer, put in some code that sends SMS messages to a Chinese subscription service, and then took some really ingenious steps to keep everything hidden from the user. That's going to happen, because everything that's electronic and popular enough is a target. The part that is concerning is that these are making their way into the Android Market.
Allow me to have a few hundred words with you about it, after the break.
Article continues belowSource: AegisLabs via Sophos; Thanks, Tony Bag o' Donuts!
I'm torn. As a user and on a personal level I say leave everything open, and force users to be diligent and only install apps they trust, regardless of where they come from. Learn what the permissions are, and why an app may or may not need them (i.e. Adobe Reader). But as a blogger and (hopefully) respected Android authority, I have a responsibility to our readers to want what's best for them. That's you guys. Many of you are respected Android authorities in your own right, and have no problem discerning what's safe and what's not. Many others aren't, and depend on Android Central and other Internet resources to offer good advice on how to stay safe. This leaves me in a bit of a pickle.
While reading the various security publications about this one, I came across a really interesting idea from Vanja Svajcer at Sophos. His idea is simple and easy to implement -- what we need is two sets of signing keys. Applications that want or need to do things like send SMS messages, or play around with your contact list should have to use a set of verified keys tied to a legitimate developer account that's been approved by Google. Let the fart apps and themes keep using user-generated keys -- don't force hobby developers to jump through any hoops for the people at Mountain View if they aren't going to be doing anything that could create a potential security issue. But the moment an app wants to access your phone book or use your GMail authToken, check the signing key and verify it. Keep the users safe, and they will stay happy. Happy users buy more apps, and more Android products. Rocket science it ain't. Vanja hit the nail squarely on the head with this one -- what say ye, Google?
Anyhoo, this one's over and done. If you're curious, here's a list of the affected applications. Do take note that they all were promptly removed from the Market and only affected users with a Chinese locale and phone number.
Get the latest news from Android Central, your trusted companion in the world of Android
- iBook
- iCartoon
- LoveBaby
- 3D Cube horror terrible
- Sea Ball
- iCalendar
- iMatch
- Shake Break
- ShakeBanger
- iMine
- iGuide
We'll keep an eye on things, and let you know the next time it happens. And there will be a next time -- the trade-off for being able to have kick-ass apps like Handcent is having apps that use the same functions and openness for things we would rather they didn't. At this point, I'm going to have to suggest two things:
- Use a "virus" scanner. Yes, I know there aren't any viruses for Android, but names sort of get stuck. All the security issues so far have required the end-user to want to install them. You won't get infected with anything just by using your phone. There are several in the Market to choose from. They all work, so check the features of each and make a choice. Then be glad we have them to do the dirty work for us.
- Don't install any apps you shouldn't be. Yes, it's tempting and we made it fairly easy with the Sideload Wonder Machine (but that was not my intent!). Security bloggers aren't just blowing smoke when they warn you about this. If you're capable, hit one of those pirate app forums and download a handful, then reverse engineer them and compare them against the official versions. If you're not capable, just trust us. About half of them have some serious differences in the code. Stick with apps you trust. Or stick to the Market -- if you do get stuck with a trojan Google will fix you up. Not only do the developers deserve the few bucks they are asking for their hard work, you'll be safer in the end.

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.
