Cloudbleed: What you need to know and what you need to do

On February 17, 2017, vulnerability researcher from Google's Project Zero Tavis Ormandy stumbled across what looked like a really nasty data leak from Cloudflare, a web performance and security company. He quickly contacted the "right" people at Cloudflare and the situation was addressed in less than an hour.
Any data breach can be significant. Especially when a service has over one billion users. We'll direct you to the Cloudflare incident report for the full details of what happened (warning: it's pretty technical). In layman's terms, data was leaked that was potentially sensitive. This data was available to anyone, even web spiders used by search engines. SSL keys were not leaked.
The Cloudflare features that used the affected HTML parser (email obfuscation, Server-side Excludes, and Automatic HTTPS Rewrites) were in use by a lot of companies. Most likely companies that you have online accounts with, This means your data may have been exposed.
Mobile Nations uses some of Cloudflare's services. In fact, you'll find us on the list floating around of sites potentially affected. We have verified that the affected services aren't in use nor have ever been used on any Mobile Nations sites.
After investigation, the features behind #Cloudbleed (Email Obfuscation, SSE, HTTPS Rewrites) have never been active on @MobileNations sitesAfter investigation, the features behind #Cloudbleed (Email Obfuscation, SSE, HTTPS Rewrites) have never been active on @MobileNations sites— Marcus Adolfsson (@madolfsson) February 24, 2017February 24, 2017
We also received notice from Cloudflare about the leak and they had this to say:
Your domain is not one of the domains where we have discovered exposed data in any third party caches. The bug has been patched so it is no longer leaking data. However, we continue to work with these caches to review their records and help them purge any exposed data we find. If we discover any data leaked about your domains during this search, we will reach out to you directly and provide you full details of what we have found.
Look for a similar statement from other places you have an account with for information about your data that may have been exposed.
What should I do
Like most big security instances, we'll never know the full details of what was and wasn't leaked out. We can confirm that we aren't using the services that were mentioned as vulnerable, but we don't know how anything else on Cloudflare's servers might have been affected. Every Cloudflare customer is in the same boat.
Get the latest news from Android Central, your trusted companion in the world of Android
That means it's time for you to get proactive.
Change the password for all of your online accounts
Yes, this sucks, but know what sucks more? Having someone get your details and have access to stuff you don't want them to have access to. Use a password manager and let it make crazy passwords and remember them for you if you don't have your own password management routine. If you haven't used a password manager in the past but wanted to check one out, now is a perfect time.
More: Best password managers for Android
Now is also a good time to remember that you should be changing your passwords regularly, which makes a password manager a must if you have a lot of accounts.
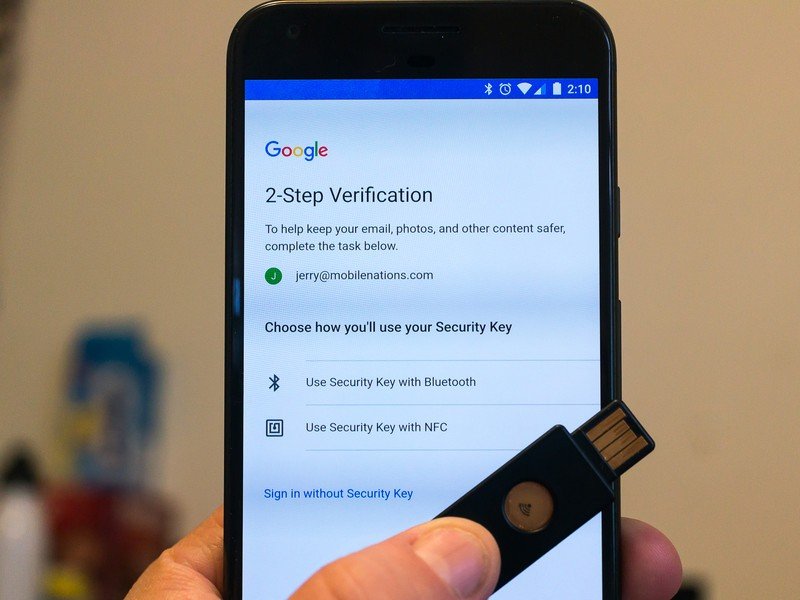
Enable two-factor authentication on every account that has it available as an option
If you have two-factor authentication enabled, someone else with your login details still won't be able to access your account. Two-factor authentication can also be a pain in the butt sometimes, but it's the best way to protect yourself when a big data breach happens, like the one we're seeing now.
Here are some resources on two-factor authentication.
- What you need to know about two-factor authentication
- How to set up two-factor authentication on your Google account
- Add a USB Security Key to your Google account
- Wireless security keys now work on Android
- Download Google Authenticator
- List of websites and whether or not they support 2FA.
Nothing we can do will prevent these kinds of data leaks. The important thing is what we can do to protect ourselves when they happen,

Jerry is an amateur woodworker and struggling shade tree mechanic. There's nothing he can't take apart, but many things he can't reassemble. You'll find him writing and speaking his loud opinion on Android Central and occasionally on Threads.

