Your Wi-Fi could betray the pin on your phone

There are lots of individual mechanisms for extracting a pin or password from a user without their knowledge. Some involve cameras, we've seen examples of guessing based on smudges on the screen, and of course if you have direct access to the phone itself there are other avenues. Adrian Croyler shared a new mechanism being used that relies on Wi-Fi interference from your hand, which is both fascinating and terrifying.
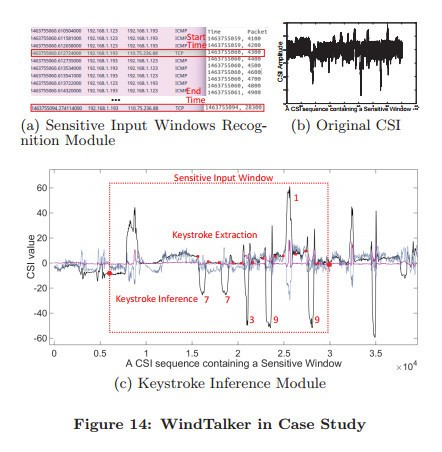
WiKey uses CSI waveform patterns to distinguish keystrokes on an external keyboard. WiPass detects graphical unlock passwords. But WindTalker is particularly effective because it doesn't require any access to the victim's phone, and works with regular mobile phones, and it piggy-backs on an existing wifi connection.
Now, there's a lot of ifs and maybes in the current implementation of this tech. You have to be connected to a Wi-Fi hotspot controller by the attacker, and some time to evaluate your usage patterns needs to be done before a precise model can be created. It's not as though every Wi-Fi network in the world is dangerous, but it does call to mind an all too often ignored personal security measure. It's important to know and trust the Wi-Fi networks you are connecting to, and with services like Google's Project Fi increasing in popularity that's happening less and less. Being connected to a strange Wi-Fi network through Google's secure VPN isn't going to protect you from this attack, because it's entirely about measuring your physical hardware once it is connected to the network.
It's still super unlikely an attack like this would be used on you in the immediate future, but if you care about your digital security this is one more reason to avoid that free Wi-Fi at Starbucks.
Get the latest news from Android Central, your trusted companion in the world of Android


